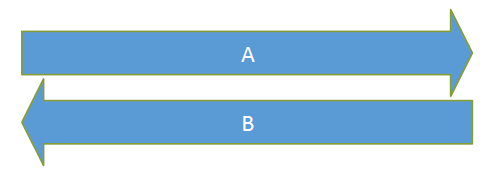
During the last few months, the concept of Perfect Forward Secrecy (PFS) was presented in many newspapers and guidelines. This concept is related to the session key generation for SSL/TLS as well as for IPsec tunnels. And even though many of these articles describe the benefit of PFS, I was still missing a picture that shows the main difference between the classical key exchange via RSA and the exchange via Diffie-Hellman with PFS. So, here comes my poster. ;)
It basically shows the two options to exchange the session key. This poster is not meant to show the cryptography behind those protocols in detail but to give an overview of the exchange of messages that are related to the session key.
The main difference is the encrypted session key that travels through the network in the case of RSA. With Diffie-Hellman (= perfect forward secrecy), the session key is derived from input of both parties and not transmitted through the Internet. Furthermore, it is freshly generated for each session. Here is the poster:
And for download as a high-quality PDF:
Side note: The user must trust the server in any case. Even if the server has set up its TLS encryption scheme with perfect forward secrecy, the user cannot prove that the server uses “good” random values for its Diffie-Hellman key generation. If, e.g., the server stores all its used random values in an unprotected file that could be accessed by a third party, the usage of PFS would be no improvement for the user. Or if the server simply uses a weak random number generator.
Links and References
Here is a shortlist of links concerning SSL/TLS and PFS:
- Software Engineer Notes: SSL in pictures
- Wikipedia: RSA (cryptosystem), Forward Secrecy, Diffie-Hellman key exchange
- Qualys SSL Labs: SSL Server Test
- TIM Trustworthy Internet Movement: Survey of the SSL Implementation of the Most Popular Web Sites
- (German) Heise Security: Forward Secrecy testen und einrichten

Thank you so much for your post!
There are so many places telling the details (or trying to) in 1000 words, but you are the first one I found who clearly states that PFS = Diffie-Hellmann (+ random numbers) and it is an alternative to public key encryption of the session key.
I wonder how few people really understand how to explain things… You are definitely amongst them!
^+1 this graph made so much sssense. thanks