I really like the kind of security features that are easy to use. The CAA “DNS Certification Authority Authorization” is one of those, specified in RFC 6844. As a domain administrator you must only generate the appropriate CAA records and you’re done. (Unlike other security features such as HPKP that requires deep and careful planning or DANE which is not used widely.) Since the check of CAA records is mandatory for CAs since 8. September 2017, the usage of those records is quite useful because it adds another layer of security.
What is CAA? In short: “CAA allows domain owners to define in a DNS record which certificate authorities are allowed to issue certificates for them“, Bulletproof TLS Newsletter #32. Hence none of your service operators is able to generate/buy a certificate at a CA that is not authorized for that name. This is useful if your company has lots of different web servers, websites, security appliances, etc., that are using TLS certificates and are managed by different persons. With CAA you can control the usage of the CAs which are allowed to sign those certificates/CSRs.
Note that the “Use of DNSSEC to authenticate CAA RRs is strongly RECOMMENDED but not
required”, RFC 6844, section 4.1. From a security perspective you should definitely use DNSSEC to have an authentic query/answer from the CAs to your DNS server.
Generate CAA Records
I added the CAA records for my test domain weberdns.de. I used the CAA Record Helper to generate them. Currently I am only using Let’s Encrypt for my domains while no wildcard certificates. Hence my CAA records are the following:
|
1 2 3 |
weberdns.de. IN CAA 0 issue "letsencrypt.org" weberdns.de. IN CAA 0 issuewild ";" weberdns.de. IN CAA 0 iodef "mailto:webmaster@webernetz.net" |
A test query with dig shows the records and the DNSSEC signature (“ad” flag at line 7 and RRSIG at line 18):
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 |
weberjoh@jw-nb15-lx:~$ dig weberdns.de caa +dnssec +multi +noauthority +noadditional ; <<>> DiG 9.10.3-P4-Ubuntu <<>> weberdns.de caa +dnssec +multi +noauthority +noadditional ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 58976 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 4, AUTHORITY: 4, ADDITIONAL: 9 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags: do; udp: 4096 ;; QUESTION SECTION: ;weberdns.de. IN CAA ;; ANSWER SECTION: weberdns.de. 2160 IN CAA 0 iodef "mailto:webmaster@webernetz.net" weberdns.de. 2160 IN CAA 0 issuewild "\;" weberdns.de. 2160 IN CAA 0 issue "letsencrypt.org" weberdns.de. 2160 IN RRSIG CAA 8 2 3600 ( 20171029091812 20170929081812 32058 weberdns.de. rlx3/ohyJjIZvOHOobcNV9UEJ+weOjsNZEcYttYCZtak bt8GZpuYfI+VK4uJIfQGlYwCmddKVZYrz513LwAosD9k JTrG5wuq3VF10sD3yP/yBWcuvI/1hNNMu+GCueB9JugU +uTNMLfdE+2p3CUhKhqX/r6d46/aKKKwfuQyhWE= ) ;; Query time: 2 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Wed Oct 04 12:05:37 CEST 2017 ;; MSG SIZE rcvd: 1303 |
Online Tests
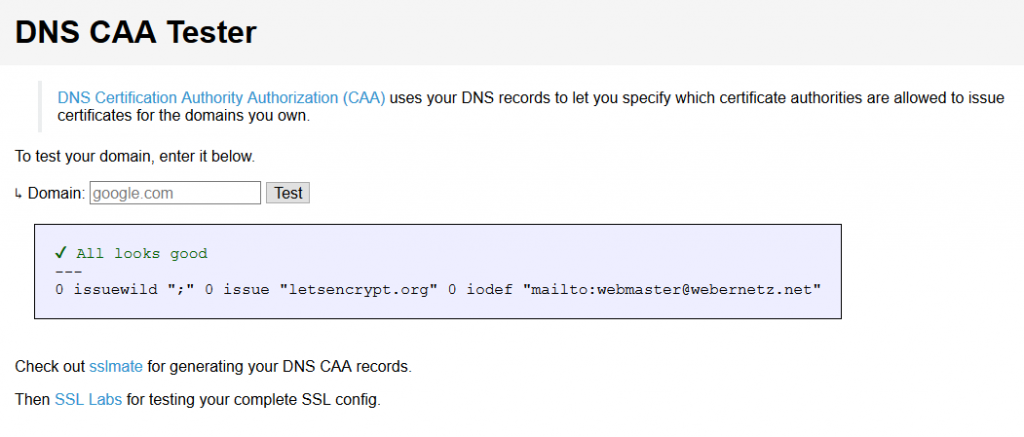
Via the online DNS CAA Tester you can verify your records via an external service. In my example this looks like this:
 Furthermore, the well-known SSL Server Test by SSL Labs also investigates the CAA records such as shown here:
Furthermore, the well-known SSL Server Test by SSL Labs also investigates the CAA records such as shown here:
Note that I have not tested any possible certificate authority whether they correctly check the CAA records. Of course not. Way too many. ;) However, this has been done by other security researchers. Hopefully they will continue discovering unreliable CAs.
Featured image “Boss on the Beach” by Adrian Scottow is licensed under CC BY-SA 2.0.



I tested for Let’s Encrypt and they do check CAAs. With a CAA for another CA, Let’s Encrypt rejects your request with:
urn:acme:error:caa “CAA record for DOMAIN_NAME prevents issuance”
what’s the effect of adding multiple SSL names in CAA?
What do you mean by “multiple SSL names”? The CAA is a record for a whole domain or a single subdomain. You can add several CAA records for each domain if you like. That is: Multiple CAs are allowed to issue certificates for that specific domain/subdomain.
Does this answer your question?
Kind regards
Johannes