Two-factor authentication is quite common these days. That’s good. Many service providers offer a second authentication before entering their systems. Beside hardware tokens or code generator apps, the traditional SMS on a mobile phone can be used for the second factor.
The FortiGate firewalls from Fortinet have the SMS option built-in. No feature license is required for that. Great. The only thing needed is an email-to-SMS provider for sending the text messages. The configuration process on the FortiGate is quite simple, however, both the GUI as well as the CLI are needed for that job. (Oh Fortinet, why aren’t you improving your GUI?)
Here is a step-by-step configuration tutorial for the two-factor authentication via SMS from a FortiGate firewall. My test case was the web-based SSL VPN portal.
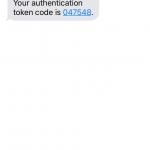
The second factor is sent via SMS. More precisely: via email2sms. That is: The FortiGate sends an email to <phone-number>@email2sms-provider.tld with the authentication code. In order to use this feature, an email server as well as an SMS service must be configured. I am not using the “FortiGuard Messaging Service” for this test but a “Custom” Email-2-SMS service from the Internet (just found via Google).
I am using a FortiWiFi 90D with FortiOS 5.2.4, build688.
Email Service
The SMTP server should be configured anyway in order to receive alert emails from the FortiGate. If it is not configured yet, it is done under System -> Config -> Advanced -> Email Service:
SMS Service
The SMS service settings are directly below the email service. Only a name and the “Domain” must be entered. This was a bit confusing for me as I saw it the first time since no other options can be set. But in fact, the FortiGate will send all SMS to <number@domain>. So it really does not need any more information. The correct domain for the mail2sms gateway is listed on the service you chose on the Internet. (I am using websms.com, a German provider.)
User
The most annoying point is to activate the two-factor SMS authentication for the user since it cannot be done through the GUI. Furthermore, if you add users, the GUI from FortiGate is not consistent in storing the phone number for local users. (As with almost all cases, the GUI from Fortinet is not that good.) So take care!
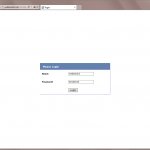
The phone number can be entered via the GUI, as well as the “Custom” SMS provider, but the only option for the “Enable Two-factor Authentication” is the Token, which we won’t use here:
Use the CLI in order to configure the following command for each user (line 3):
|
1 2 3 4 |
fd-wv-fw04 # config user local fd-wv-fw04 (local) # edit weberjoh2 fd-wv-fw04 (weberjoh2) # set two-factor sms fd-wv-fw04 (weberjoh2) # next |
After that, the two factor auth method “sms” is shown in the summary as well as under the users details:
That’s all for the config.
Test
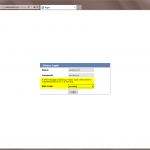
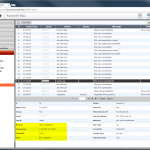
My use case for the two-factor authentication is the web-based SSL VPN. Following are the screenshots I’ve made during the logon process, as well as the log events:
The corresponding log messages on the CLI look like this:
|
1 2 3 |
23: date=2015-12-03 time=17:23:16 logid=0100038411 type=event subtype=system level=notice vd="root" logdesc="Two-factor authentication code sent" user="weberjoh2" action="send authentication code" msg="Send two-factor authentication token code 047548 to 004********211@email2sms.websms.com" 24: date=2015-12-03 time=17:23:16 logid=0101039943 type=event subtype=vpn level=information vd="root" logdesc="SSL VPN new connection" action="ssl-new-con" tunneltype="ssl" tunnelid=0 remip=87.159.185.106 tunnelip=(null) user="N/A" group="N/A" dst_host="N/A" reason="N/A" msg="SSL new connection" |
I like it. Easy to use, even for non-technical persons. ;)
[Update] SMS Expiry
After I implemented this feature by some customers I got some tickets in which users were complaining about login failures. I figured out that these failures were related to the short SMS expiry of 60 seconds. Since the token path via email and SMS takes some time, I recommend to increase the expiry to 120 seconds:
|
1 2 3 |
config system global set two-factor-sms-expiry 120 end |
Works better now.
Links
- Fortinet: Technical Note: SMS Two Factor Authentication in FortiGate
- Wikipedia: Two-factor authentication
Featured image “Handy” by Jeremy Brooks is licensed under CC BY-NC 2.0.




Good guide, thank you. However Fortigate makes sender address the same as recipient and this causes a problem. Emails sent to number@domain appeared from the same number@domain. This triggers anti spoofing policy on our antispam filter and I had to create the policy to bypass it. Another issue was the SMS provider (I tried 2 different and the issue was the same) had to have number@domain added in their allowed email addresses for this to work.
Some one is steeling your stuff:
https://blazenetit.blogspot.ch/2018/01/fortigate-2-factor-authentication-via.html
Oh, thanks for giving me the notice. I have emailed him.
It is not the first time that someone steals my blogposts. To my mind this is a part of the Internet … ;(
awesome article, thanks for the great info. Worked like a charm :) I’m looking to expand my fortinet contacts so please reach out if you’re ever interested in consulting
is it possible for the user – when logging in i.e. on the VPN – to choose to use the token generated by the app or a token to be received via SMS?
I don’t know. But I don’t think so.
Thanks for your reply! :)