I want to talk about a fun fact concerning my blog statistics: Since a few years I have some “CLI troubleshooting commands” posts on my blog – one for the Palo Alto Networks firewall and another for the FortiGate firewall from Fortinet. If you are searching on Google for something like “palo alto cli commands” or “fortigate troubleshooting cli” my blog is always listed amongst the first 2-4 results.
But for some reasons the article for Fortinet has much more hits. I don’t know why but I have two different ideas. What do you think?
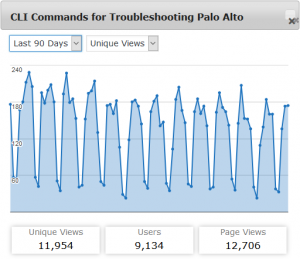
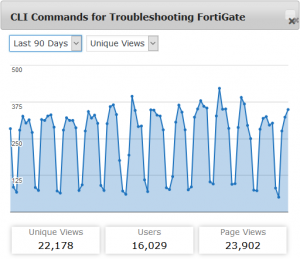
Let’s have a look at the stats. Following are two screenshots from my Google Analytics widget over 90 days that show about 12k views on the Palo and 22k views on the Forti blogposts. The averages per day are about 132 views for Palo while 246 views for Forti.
So, how can we explain these differences?
Interpretation 1: Fortinet has more firewalls out there
This might be obvious: If Fortinet sells more firewalls around the world, more admins must troubleshoot them, hence more views. Simple result: Palo Alto has not sold that much firewalls.
But this relies on the assumption that both firewalls need the same amount of CLI troubleshooting, which is not the case, hence:
Interpretation 2: FortiGates need more CLI troubleshooting
Comparing the two “next generation firewalls” just about the troubleshooting possibilities you will see that you can gather lots of information directly from the GUI on the Palo Alto while you must use some CLI commands on the FortiGate.
You want to know your OSPF neighbors and counters? -> Palo: GUI, FortiGate: CLI.
You want to show the used ciphers for IPsec VPN sessions? -> Palo: GUI, FortiGate: CLI.
You want to find out which LLDP neighbors are connected? -> Palo: GUI, FortiGate: CLI.
And even when you are comparing the CLI commands you have to deal with get, diagnose, execute, show on the Forti while Palo Alto almost uses show . Or you can use the find command keyword ... command on the Palo to actually find your command. ;) Great feature.
Hence: My FortiGate CLI troubleshooting cheat sheet has more hits since more admins actually MUST use the CLI compared to Palo Alto.
So, what do you think? I am really interested in some other opinions. Please write a comment if you have one. And don’t take it too serious. ;) Cheers.
Featured image: “Le Dernier Combat, Acte V” by @mopictures is licensed under CC BY-NC-ND 2.0.


How is Palo Alto and Fortinet compare to Sophos? In terms of reliability and popularity?
One possibility is that Fortinet has been around longer than Palo Alto. Another is cost – Palo Alto seems to be on the expensive side.
Other considerations: The quality of their documentation, stability of features, quality of their community forums, etc. Love the blog, though – keep it up!
@John, you can compare all of the major Next generation firewall vendors on https://www.techpillar.com/network-security/firewall.
Hallo Johannes,
meine erste Fortigate war eine Fortigate 50 (gekauft 19.03.2004), danach eine 50B, aktuell eine 60D unter Fortios 5.6.0 und 90D Fortios 5.2.11.
Ich muss sagen, dass sich beim Fortios von Version 2.5 bis Version 5.2.11 leider die GUI nicht alle Einstellungsmöglichkeiten bietet und man daher man immer CLI braucht. Somit die Erklärung warum viele nach Befehlen suchen, die ja doch eine eigene Syntax haben.
Mit Fortios 5.4 und neuer wird das jetzt etwas besser. Und vielleich weniger wichtig.
Dennoch ist Fortigate schon lange weltweiter Marktführer bei UTM.
(2004) https://www.pressebox.de/pressemitteilung/fortinet-gmbh-frankfurt-am/IDC-Fortinet-weiter-Marktfuehrer-im-Unified-Threat-Management/boxid/32947
(2008) http://www.netit.at/aktuell/archiv/ansicht//artikel/fortinet-weltweit-no1/
(2014) http://www.ingentive.net/kompetenzen/fortinet
Beachtlich, wenn man bedenkt, dass die Firma erst um 2000 gegründet wurde!
PS: Danke für Deinen Artikel in der letzt c´t.
Weiter so! Liebe Grüße
Martin
I’m someone who works with Palo Alto firewalls and Juniper SRX, I am trying to learn FortiGates and finding them.. complex to be honest.
Part of it I think is they actually have a significant number of features that PA do not such as the ability to be a DNS server, do agentless device detection, be an explicit proxy, WiFi, etc.
And another part of it I suspect is with FortiGate being older, their products seem to have a lot of gotchas and “normally do this, but in this case do that” type of scenarios whereas PA being a newer design suffer less of that. An example is the UTM feature which is sort of bolted onto the firewall policies.
Another is naming. FortiNet will call something X in the documentation, Y at the GUI and Z at the CLI. Annoys me a bit.
My 2 cents:
– Fortinet share of market is much bigger – Gartner has some stats for sure
– Fortinet (again see above) has bigger price range, from relatively cheap 30, 60 .. up to the monsters, while PA starts at a higher price mark so SMB clients shy away from it.
– Fortinet get on our nerves changing with every OS release location of commands/GUI/names, I personally debug FGs ONLY on CLI, some configs do there as well, instead of re-learning GUI each new release.
– PA has better consistency history with browsers, in FG you are never sure when GUI is missing something whether it is because it is not there or some browser compatibility issue just plain hides it.
– On a personal note, my blog is mostly about Checkpoint and so ranked in Google quite high on that, but a dozen or so posts about Fortigate get the same or even more views than most popular Checkpoint posts.
BR
Yuri
PA documentation, live forums and their tac is much quicker to resolution than forti in my opinion.
When you have hundreds of pa firewalls you quickly pick up the search engine parameters to look for after a while. If you don’t get a hit on the forums/google/pa kb you open a case and a pa engineer will contact you in less than an hour.
The pa does have some issue when you scale globally I will admit, but for the most part, it is very well documented. It is relatively easy to determine when something is a self-inflicted problem or something caused by a bug.
With the forti’s from my perspective may be different than others, but I can only speak to my experiences. The forti documentation is iffy, most admins stay in the gui unless they MUST go to the cli and the documentation seems a bit more unorganized. I know when I look for something I will remove the manufacturer from the query to find a hit.
+cisco +dmvpn +vrf -“cisco.com”
+fortinet +ipseec -“fortinet.com”
By removing the endless pages of technical documentation from the last ten years, you wind up on a blog. Eventually, you will hit a wall with your results and you try and come up with a really common query to get a useful result.
I wound up here based on searching for a way to set my fans on my pa-500’s to a level less than a JET ENGINE.
palo alto pa-500 fan speed
I still have jet engines :)