This is a small example on how to configure policy routes (also known as policy-based forwarding or policy-based routing) on a Fortinet firewall, which is really simple at all. Only one single configuration page and you’re done. ;)
(Compared to my other PBR/PBF tutorials from Juniper ScreenOS and Palo Alto Networks, there is only one screenshot needed to explain the policy route. Ok, it is not that flexible, but easy.)
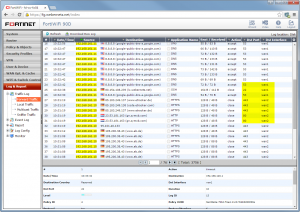
In my lab, I have a static default route to the wan1 interface. On the wan2 interface, there is a simple DSL connection to the Internet which shall be used for http/https traffic from the users. That is: Everything from the users IP segment (192.168.161.0/24) to the destination ports 80 and 443 shall be forwarded to this DSL connection. But an exemption is still needed: If the destination is on the internal LAN, the connection should not be policy routed. (Of course, appropriate policies must be in place, too.) The configuration is done under Router -> Static -> Policy Routes:
That’s it. In the Forward Traffic Log, it is easy to see which destination interface is used, dependent on the destination port:
Featured image “DSCF1762” by Ronald Redentor de Veyra is licensed under CC BY-NC 2.0.



Hello,
Thanks a lot for your tuto but where is this option in V5.4 ?
Router doesn’t exist …
Hi Nicit,
you probably have not enabled the feature under System -> Config -> Features -> Advanced Routing. Note that these settings only enable/disable the GUI sections while the actual features are enabled everytime.
After that your “Router” sections should be present again.
if i use switch mode for internal / lan, then i create vlan on that, how to create routing from vlan to internal ?
Hi djoun,
I can’t see what you mean. If you have local configured networks (regardless of which kind, vlan, lan, internal, whatever) NO additional routing must be created since all networks are in the routing table automatically. You should see all the attached networks in the routing table.
(Don’t forget the security policies prior to send traffic.)
Hi,
Can I use policy routes to “override” the internal routing table?
I’ve got a server that needs to talk to a network (over vpn)
The ip-space on that network overlaps with that of a local vlan (not the one that the server is on)
The server does not need to talk to the local vlan, so I figured I could just use a policy that looks like this:
x.x.x.10(server) -> y.y.y.0(remote network) via. vpn-interface.
Flow Trace shows that it is still trying the local vlan interface for traffic destined to the ipsec interface.
Any thoughts?
You can move the “except”-rules to the top. I.e. set action deny for the items that should not be policy routed.
Hey Hans,
yes indeed, you can use policy routes for that. They will override the normal routing table. However, I am not quite sure if this is the case for “local connected” networks, since your local vlan interface is LOCAL and not only a “route”. Maybe you must google for that? (Or double check the policy route configuration ;))
Cu,
Johannes
Hey!
I had to do the following to get the results I wanted.
1. Create a static route for the attached network (vlan).
2. re-config the vpn as a policy based vpn and not interface/route based.
3. apply policy based routing as needed.
Only then would the traffic from the server be affected by policy based routing.
Regards,
Hans
If Cisco device omitted crypto map then we are getting ping peer IP of the physical interface but when established crypto map in IPsec we can’t ping peer IP but also ipsec phase one us up but phase2 in not up.
I’m missing a sketch here….