VoIP calls, using the network protocols SIP/SDP and RTP, are the de-facto standard when it comes to voice calls. Wireshark offers some special features to analyze those calls and RTP streams – even with a nice “Play Streams” option, which discretely decodes your calls. Ouch. Again and again, frightening which privacy-related protocols are completely unencrypted on the Internet!
Here are some hints for Wireshark as well as a downloadable pcap with three calls in there. ;) Have fun!
I won’t explain any SIP/SDP/RTP details here. There is much information out there already. I basically want to share a pcap to play with, along with some Wireshark screenshots.
Download the pcap, 7zipped, 473 KB:
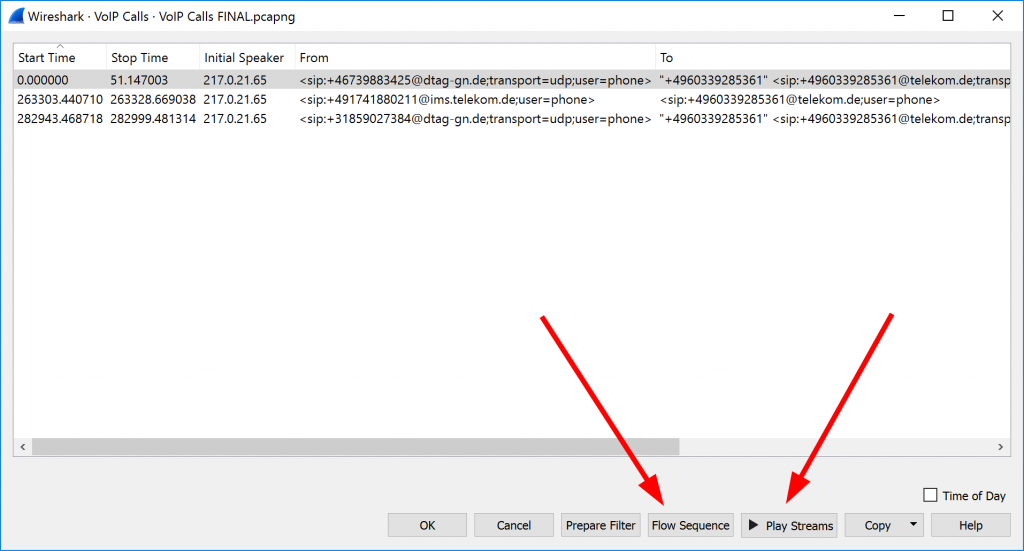
Open it with Wireshark and go to Telephony -> VoIP Calls to get this overview:
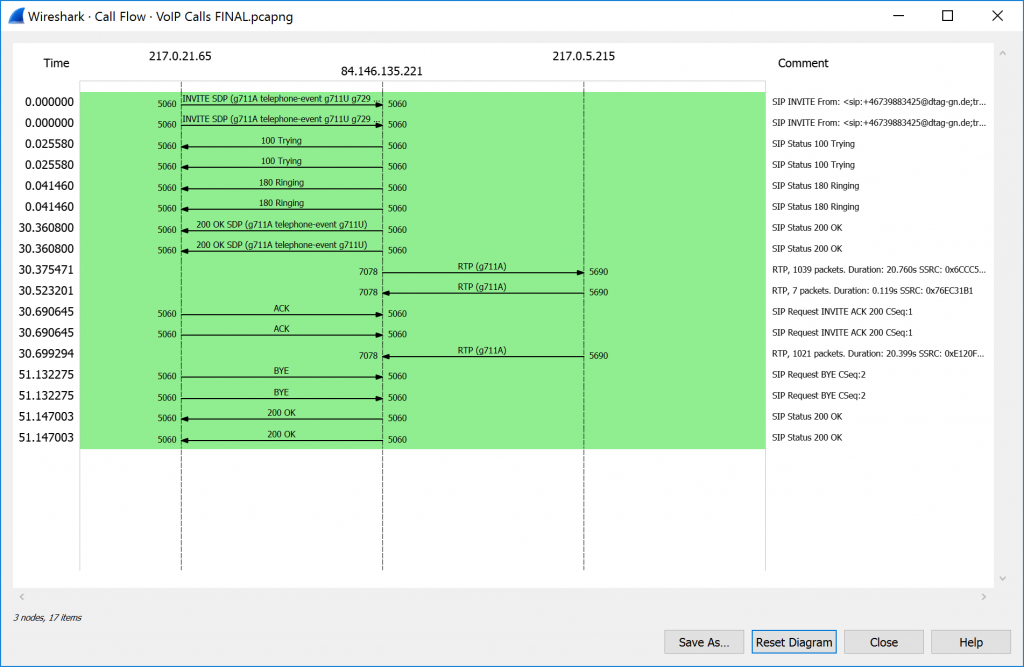
You can either have a look at the Flow Sequence:
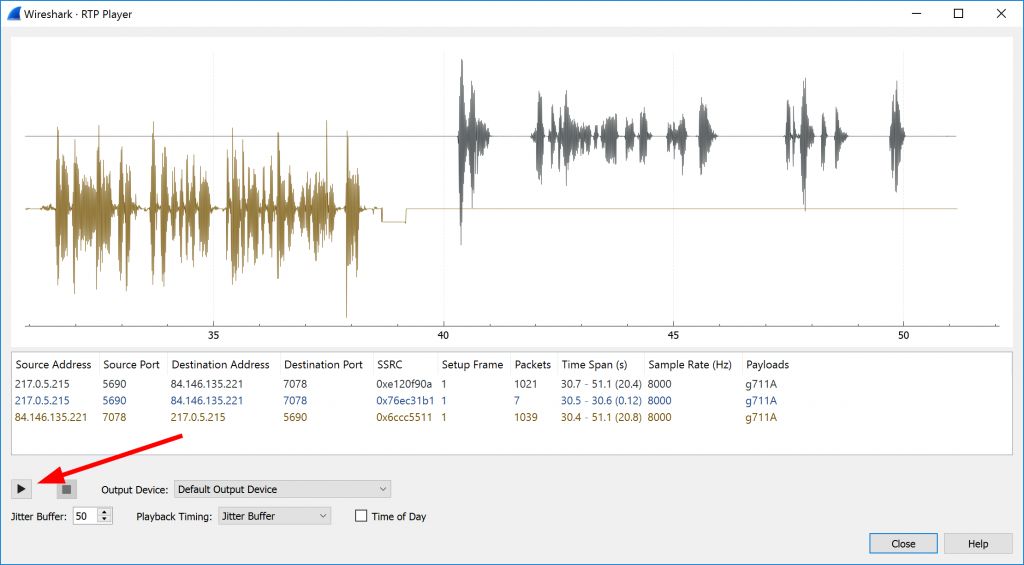
Or you hit the “Play Streams” button to actually listen to the calls in the RTP Player. Wuh:
I have three VoIP calls in the pcap. Two g711A streams and one HD stream with g722.
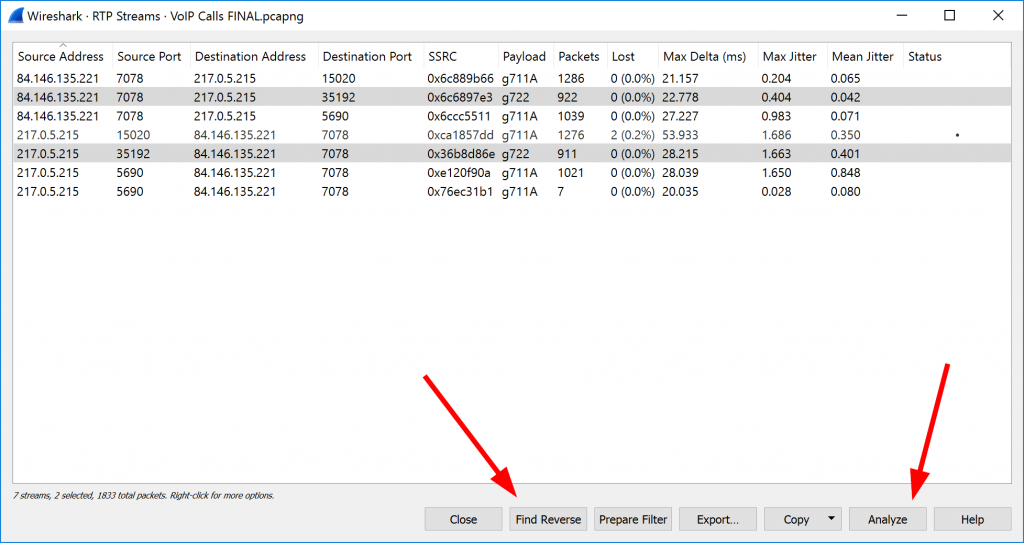
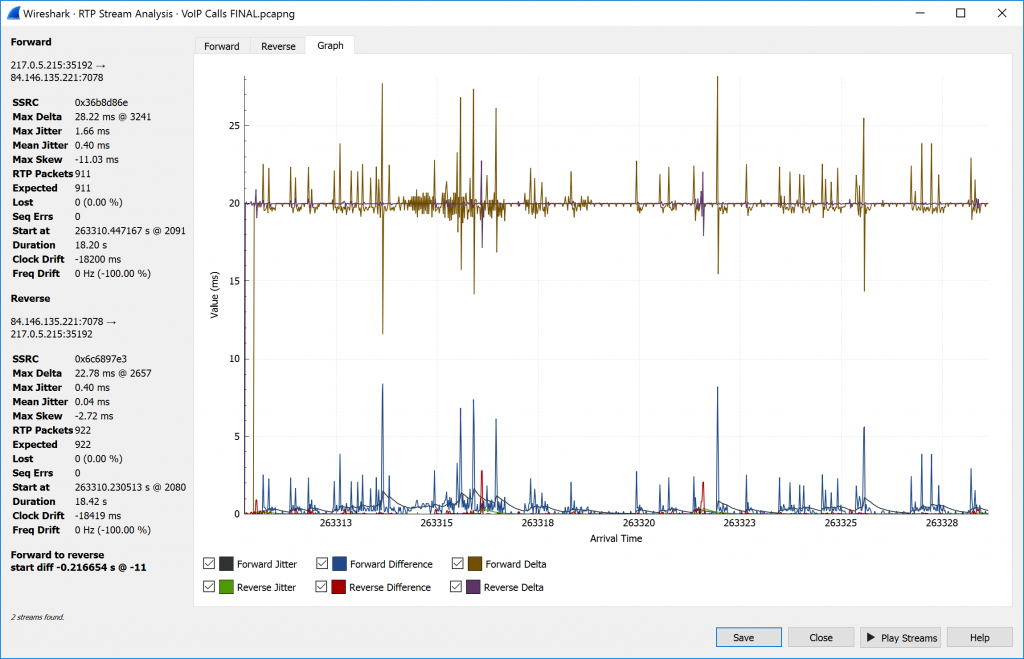
Another way to have a look at the RTP details is to open Telephony -> RTP -> RTP Streams, click the stream of interest, followed by “Find Reverse” and then Analyze:
This gives you details about the jitter, losses, etc.:
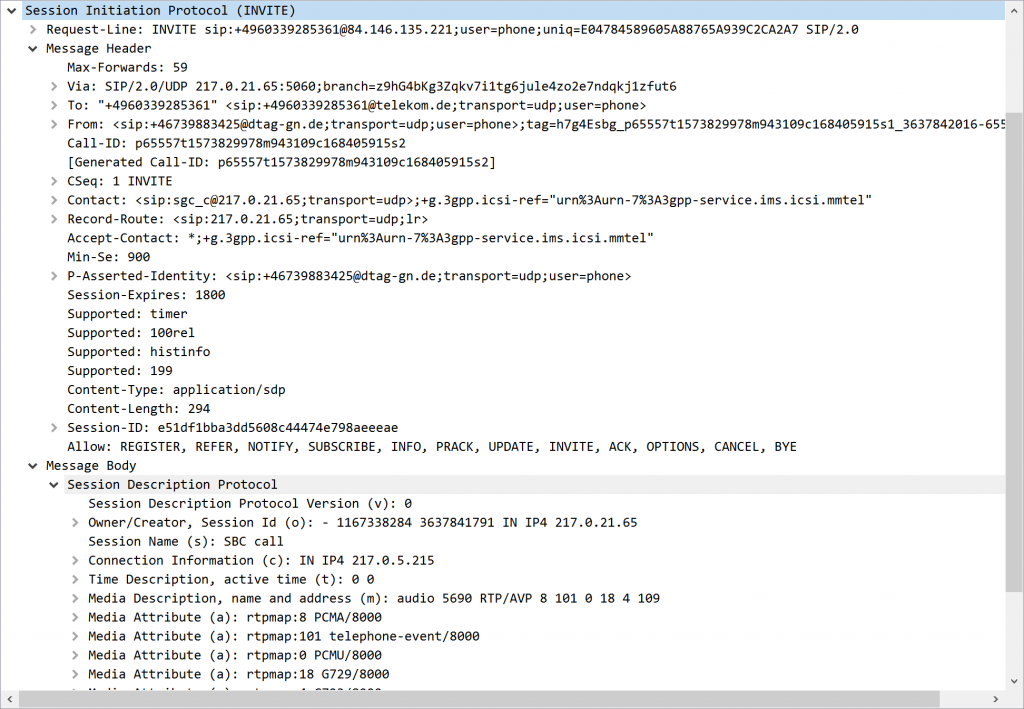
Of course, the great Wireshark dissectors work for all protocol details as well, e.g., the SIP packet details:
Featured image “Tischfernsprecher W48” by Felix Winkelnkemper is licensed under CC BY 2.0.


Hi Johannes, this is a great example. I was wondering why there is no RTCP communication in the capture?
Uh, good question. I have absolutely no idea. ;) Do you have any other samples of VoIP traffic that is using RTCP?
Hi Johannes,
thanks for the public provided Wireshark VoIP capture.
We did use it as example for our Stacked Brains VoIP Analyzer Tool to show the way our tool converts any VoIP Wireshark capture to nicely formatted HTML pages.
You can find your processed example at https://www.voipanalyzertool.com
under the “output” section.
Our tool is able to merge hundreds of Wireshark captures to one single Wireshark capture, filter intelligent, audit Wireshark VoIP captures and as last, convert any Wireshark (VoIP) capture to an anonymous Wireshark capture (obfuscate) where SIP names, SIP call numbers and/or IP addresses are re-written.
Thanks once more for the public available Wireshark VoIP capture.
It was useful for us.
The Stacked Brains Team
Thanks for the article. I would like to know the identity of the three parties shown in the sequence diagram, which is which? the call is held between two participants, which is the third?
Hey Sohaib. The three calls (and their IDs and so on) are listed in the very first screenshot of this post. Within Wireshark, it’s Telephony -> VoIP Calls.
Or are you searching for something else?
Hey thanks for the capture! it helped.
I have no idea what the client said but a simple voice to text says this ( I thought it sounded German but it’s dutch):
Hallo! Dit is zaken van Summit. Heb je mijn Tweetie tool gedownload? Ga naar gate twee dubbelpunt slash lees. Euh Singer Ik en mijn b punt idee C les cheatsheet. Veel succes! doei!
Translate2Eng:
Hello! This is Summit business. Have you downloaded my Tweetie tool? Euh Singer Me and my b point idea C lesson cheatsheet. Good luck! Bye!