I tested the Palo Alto GlobalProtect app on my iPhone, but also the native IPsec Cisco VPN-Client on iOS which connects to the GlobalProtect Gateway on a Palo Alto firewall, too. Since this variant needs no further licenses from Palo Alto, it is a cheap alternative for a basic VPN connection.
Though not that much exciting, there are a few differences in the logs on the firewall which I will show here on the basis of a few screenshots.
During these tests, I ran PAN-OS 6.0.1 with a GlobalProtect Agent of 2.0.1. My iPhone ran iOS version 7.0.6.
The GlobalProtect app from Palo Alto works without any problems if a correct Portal and Gateway are already configured. In order to use the native Cisco IPsec client on iOS, the “X-Auth Support” must be enabled on the GlobalProtect Gateway, such as shown here in my post about the Linux vpnc client.
GlobalProtect vs. iOS IPsec Client
In order to have the best performance and configuration possibilities, the GlobalProtect app from Palo Alto should be used. With this app, options such as HIP profiles can be used, the best Gateway can be determined after a connect to the Portal, etc. However, it requires the GlobalProtect Gateway license [reference].
So, if only the mere VPN connection to the internal network is needed, the built-in IPsec VPN-Client from Cisco fits completely. It uses the IKE and ESP protocols (instead of SSL) to connect to the Gateway firewall.
Here are two screenshots of both variants from the iPhone. Since the configuration steps are really simple (only the gateway, groupname & -password are needed), I am not showing them here in detail.
PA: Remote Users Log
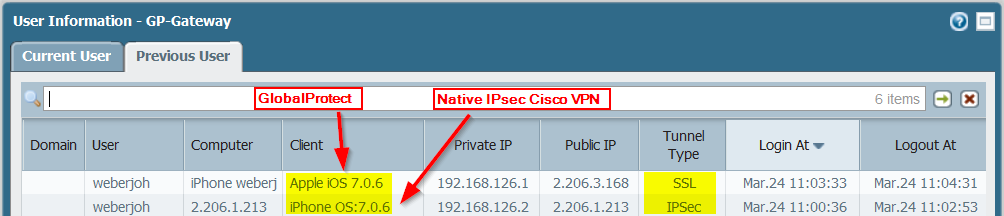
Here are the log differences on the Gateway -> Remote Users information page. If a user logs in with the GlobalProtect app, the client is recognized as “Apple iOS …”, while a native IPsec connections is shown as “iPhone OS: …”:
PA: System Log
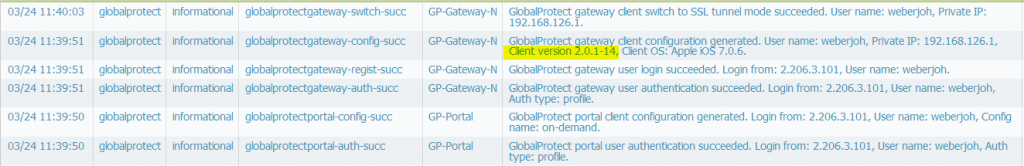
The System Logs under the Monitor tab are a bit more different. Here is the GlobalProtect log with much more lines compared to the IPsec logs beneath. This is because the app first connects to the Portal and then to the Gateway:
These are the native IPsec System logs with a direct connection to the Gateway:
Further Reading
- Palo Alto: GlobalProtect Licenses
- Palo Alto: GlobalProtect Configuration Tech Note
- Palo Alto: GlobalProtect Configuration for the IPsec Client on Apple iOS Devices
Featured image “Millenium Bridge” by Mariano Mantel is licensed under CC BY-NC 2.0.




Great information and very accurate. Is anyone aware of a Android client that will work separately?
The native Android “Basic VPN” client works for our PA. Set up the connection to use the IPSec Xauth RSA option.
Thanks for the writeup!
Have you tried IKEv2 now that it’s available (and mostly bugfixed) in PanOS 7.0.5 and iOS 9?
I can’t get them to work in iOS or Android in version 7.1.0.
yes me too.it is not working with 7.1.0
There’s a bug on 7.1.x. Use the CLI to fix it.
# set global-protect global-protect-gateway YOUR_GP_GATEWAY_GOES_HERE client-auth auth-any os Any
Apparently, the Web GUI puts another setting you can’t see unless you display it using the CLI.
RaulTrujillo
I tried with PanOS 6.1.14 and IOS 10 it is not working ios gets an error “The VPN server did not respond “