Another small post out of my “At a Glance” series: The different types of virtual private networks (VPNs). Looking at Site-to-Site and Remote Access VPNs.


Another small post out of my “At a Glance” series: The different types of virtual private networks (VPNs). Looking at Site-to-Site and Remote Access VPNs.

Probably the biggest prejudice when it comes to IPv6 is: “I don’t like those long addresses – they are hard to remember.” While this seems to be obvious due to the length and hexadecimal presentation of v6 addresses, it is NOT true. In the end, you’ll love IPv6 addresses in your own networks. This is why – summed up in one poster:

Working with Infoblox can be challenging when it comes to their naming of features, licenses, marketing slides, and GUI options. So let’s bring some clarity into this chaos. :D I have listed the most common DNS security features and their corresponding Infoblox names. I hope you folks can use it as well.
Continue reading Infoblox Features & Licenses Naming Clarity

As a network administrator I know that there are SSH fingerprints. And of course I know that I must verify the fingerprints for every new connection. ;) But I did not know that there are so many different kinds of fingerprints such as md5- or sha-hashed, represented in base64 or hex, and of course for each public key pair such as RSA, DSA, ECDSA, and Ed25519. Uh, a bit too complicated at a first glance. Hence I draw a picture.

I wanted to configure a weekly email report on a Palo Alto Networks firewall. “Yes, no problem”, I thought. Well, it was absolutely not that easy. ;(
While the PAN firewalls have a great GUI and a good design at all they lack an easy-to-use email reporting function, especially when compared to the FortiGate firewalls which have a great local report feature. –> If you want some stats on a weekly basis you must configure it completely from scratch. Unluckily this is not that easy since you must pass several steps for that. Therefore, I drew an outline of the Palo Alto reporting stages to have an overview of them.

MIP DIP VIP. I am sometimes confused with the NAT names of the Juniper ScreenOS devices. Therefore, I drew a small figure with a few basic examples for these NAT types.

For a beginner, the configuration of a Juniper Secure Access SA/MAG Pulse Connect Secure device is not that simple. There are too many options and links that must be filled in. Though there are quite detailed configuration guides I was missing a “quick start” figure to see which profiles, roles, etc. must be set in order to have a simple login and group membership environment.
Here comes my at-a-glance poster for the Pulse Connect Secure SSL-VPN gateway.
Continue reading Pulse Connect Secure: Easy Deployment Poster

I missed a sequence diagram for DHCP which not only shows the four basic messages (DISCOVER, OFFER, REQUEST, ACK), but also the used source/destination addresses and ports, the type of connection (unicast/broadcast), the differences between the initial and the renewing messages, and the needed firewall rules for allowing DHCP traffic to/from the own interface or to/from a DHCP relay agent.
Here it comes! :)
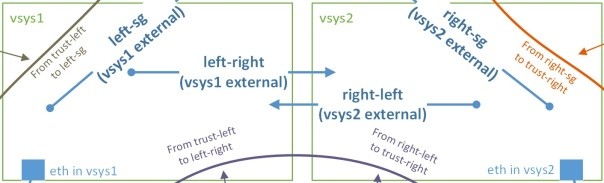
It was not easy for me to understand the type of zones and “from – to” policy definitions when working with a Palo Alto firewall that has multiple vsys’s and a shared gateway. I was missing an at-a-glance picture that shows which zones to use. (Though this document describes the whole process quite good.) So, here it comes…
Continue reading Palo Alto: Vsys & Shared Gateway – Zones, Policies, and Logs
During the last few months, the concept of Perfect Forward Secrecy (PFS) was presented in many newspapers and guidelines. This concept is related to the session key generation for SSL/TLS as well as for IPsec tunnels. And even though many of these articles describe the benefit of PFS, I was still missing a picture that shows the main difference between the classical key exchange via RSA and the exchange via Diffie-Hellman with PFS. So, here comes my poster. ;)

I am currently in touch with a few HTTP proxy installations. As every time when troubleshooting network issues, I am looking at Wireshark on the network and trying to understand the different packets.
Here is a short overview of the differences between HTTP requests that are sent directly to the destination and HTTP requests that are sent via a proxy. Wireshark screenshots and a downloadable pcap round things up.
Continue reading At a Glance: HTTP Proxy Packets vs. Normal HTTP Packets

I am always struggling with the definition of a “false positive” though it should be easy. Since I love figures that point out the most important facts I drew one concerning the false positive etc. structure. It is based on the example of a malware detection in which an engine decides whether a piece of software is a malware or not. Here it is: