Meine Kids spielen derzeit häufig Brawl Stars, ein Echtzeit Onlinespiel. Und sie schauen auch immer mal Videos dazu, bei denen ihnen jetzt der Floh ins Ohr gesetzt wurde, dass man ein iPad ja auch per LAN-Adapter mit einem Netzwerkkabel ausstatten kann, was ja den Ping verbessert.
JAAAA, endlich waren meine Kenntnisse in Sachen Netzwerktechnik mal von meinen Kindern gefragt. “Papa, weißt du, was ein LAN-Kabel ist?” “Ja klar.” “Hast du so eines?” “Ja, circa Hundert.” “Waaas? Echt jetzt? Dann muss ich mir ja gar keins kaufen.” 😂
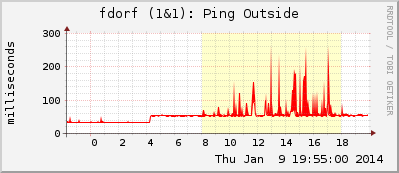
Neben der Subjektivität, ob das Zocken per LAN-Kabel jetzt merklich besser wird, wollte ich mal objektiv messen, wie sich die Latenz eines per Ethernet-Adapter angeschlossenen iPads denn nun wirklich verhält. Wie viel besser wird der Ping im Idle- bzw. im Volllastfall? Was sagt die Laufzeit zum Default Gateway? Hier ein paar Tests: