A common misunderstanding of traceroute is that it fully relies on ping. “If I block ping at my firewall, no one can use traceroute to reveal my internal routing path”. Unfortunately, this is not true. If traceroute is used with TCP SYN packets on permitted TCP/UDP ports, all intermediary firewalls will handle the IP packets with TTL = 0 corresponding to the RFCs and will reply with an ICMP time exceeded packet to the source.
In this post, I am listing an example that uses traceroute with TCP port 25 (SMTP) to traverse a firewall. A sample pcap file can be downloaded while some Wireshark screenshots show a few details.
Traceroute is not Ping
The basis to understand is that traceroute is NOT ping though it is commonly sent via ICMP echo requests. The core of traceroute is that routers are decrementing the hop count (TTL) in the IP header which is independent of the upper layer protocol! By using traceroute, it starts with a TTL of 1 and increments it after every packet. The IP packets that are used for traceroute can either transport ICMP echo requests or any other (!) protocol such as UDP or TCP. In the latter case, TCP SYN packets on a specific destination port, e.g., 80 for HTTP, are sent.
The answers of middle routers that traverse back to the host are ICMP time exceeded messages. (Wikipedia: Traceroute, Time to Live (Hop Limit), ICMP Time Exceeded.)
Traversing Firewalls
Consider a firewall that resides between the Internet and a DMZ. In the DMZ, a web server listens on port 80 and the firewall permits that port. No other services are allowed through the firewall. That is: Ping is denied and therefore a traceroute with ICMP echo requests is denied, too. BUT: Since TCP on port 80 must be allowed in order to use the web server, a traceroute with TCP SYN on port 80 will succeed. (Though there might be situations in which an administrator blocks the handling of time exceeded packets explicitly.) That is: You have an option to reveal the internal routing path though ping was denied.
Example
I am using a Linux computer with the traceroute command. Without any options, it uses some UDP high ports. “-I” forces it to use ICMP echo-request packets. “-T” uses TCP SYN packets that can be set to a specific port with “-p “. The same can be used for UDP “-U“.
Here is an example in which I issued three different traceroutes to my mail server:
- plain traceroute: no final response since dynamic UDP ports are not allowed
- traceroute with ICMP: ditto
- traceroute on TCP port 25 (smtp): reveals all hops :)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 |
pi@jw-pi01 ~ $ traceroute mail.webertest.net traceroute to mail.webertest.net (80.154.108.237), 30 hops max, 60 byte packets 1 fritz.box (192.168.86.1) 6.863 ms 6.546 ms 6.286 ms 2 rdsl-frnk-de80.nw.mediaways.net (213.20.56.15) 26.694 ms 26.391 ms 26.107 ms 3 xmwc-frnk-de05-chan-20.nw.mediaways.net (213.20.251.69) 30.259 ms 29.940 ms 34.017 ms 4 rmwc-frnk-de01-chan-6-0.nw.mediaways.net (62.53.0.105) 33.775 ms 33.528 ms 33.276 ms 5 213.140.50.124 (213.140.50.124) 55.764 ms 55.475 ms 55.312 ms 6 80.150.168.5 (80.150.168.5) 55.031 ms 51.767 ms 51.498 ms 7 f-sb1-i.F.DE.NET.DTAG.DE (62.154.15.9) 51.331 ms 50.949 ms 55.120 ms 8 f-eb1-i.F.DE.NET.DTAG.DE (62.154.16.238) 54.776 ms 46.659 ms 50.756 ms 9 0180506-1-1-gw.F.DE.NET.DTAG.DE (80.148.112.46) 50.421 ms 50.269 ms 49.984 ms 10 80.154.108.226 (80.154.108.226) 49.758 ms 52.294 ms 56.354 ms 11 * * * 12 * * * 13 * * * 14 * * * 15 * * * 16 *^C pi@jw-pi01 ~ $ sudo traceroute -I mail.webertest.net traceroute to mail.webertest.net (80.154.108.237), 30 hops max, 60 byte packets 1 fritz.box (192.168.86.1) 7.859 ms 7.739 ms 7.559 ms 2 rdsl-frnk-de80.nw.mediaways.net (213.20.56.15) 31.035 ms 30.847 ms 30.786 ms 3 xmwc-frnk-de05-chan-20.nw.mediaways.net (213.20.251.69) 30.574 ms 30.512 ms 34.618 ms 4 rmwc-frnk-de01-chan-6-0.nw.mediaways.net (62.53.0.105) 34.480 ms 34.384 ms 34.229 ms 5 213.140.50.124 (213.140.50.124) 58.563 ms 58.419 ms 58.289 ms 6 80.150.168.5 (80.150.168.5) 62.472 ms 45.730 ms 49.122 ms 7 f-sb1-i.F.DE.NET.DTAG.DE (62.154.14.133) 57.580 ms 55.163 ms 49.804 ms 8 f-eb1-i.F.DE.NET.DTAG.DE (62.154.16.238) 53.909 ms 48.460 ms 47.681 ms 9 0180506-1-1-gw.F.DE.NET.DTAG.DE (80.148.112.46) 46.931 ms 47.910 ms 51.173 ms 10 80.154.108.226 (80.154.108.226) 54.092 ms 53.816 ms 52.535 ms 11 * * * 12 * * * 13 * * * 14 * * * 15 * * * 16 *^C pi@jw-pi01 ~ $ sudo traceroute -T -p 25 mail.webertest.net traceroute to mail.webertest.net (80.154.108.237), 30 hops max, 60 byte packets 1 fritz.box (192.168.86.1) 9.233 ms 9.055 ms 13.059 ms 2 rdsl-frnk-de80.nw.mediaways.net (213.20.56.15) 32.008 ms 31.831 ms 31.621 ms 3 xmwc-frnk-de05-chan-20.nw.mediaways.net (213.20.251.69) 31.352 ms 35.440 ms 35.233 ms 4 rmwc-frnk-de01-chan-6-0.nw.mediaways.net (62.53.0.105) 35.015 ms 34.874 ms 34.666 ms 5 213.140.50.124 (213.140.50.124) 60.108 ms 59.849 ms 59.669 ms 6 80.150.168.5 (80.150.168.5) 63.793 ms 47.955 ms 51.132 ms 7 f-sb1-i.F.DE.NET.DTAG.DE (62.154.14.213) 60.101 ms 52.755 ms 55.931 ms 8 f-eb1-i.F.DE.NET.DTAG.DE (62.154.16.238) 54.791 ms 53.492 ms 52.380 ms 9 0180506-1-1-gw.F.DE.NET.DTAG.DE (80.148.112.46) 51.405 ms 50.434 ms 49.511 ms 10 80.154.108.226 (80.154.108.226) 48.593 ms 52.392 ms 50.294 ms 11 mail.webertest.net (80.154.108.237) 53.276 ms 58.050 ms 56.910 ms 12 mail.webertest.net (80.154.108.237) 60.058 ms 53.708 ms 52.386 ms |
Of course, the same is true for IPv6:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 |
pi@jw-pi01 ~ $ traceroute -6 mail.webertest.net traceroute to mail.webertest.net (2003:51:6012:110::15), 30 hops max, 80 byte packets 1 fritz.box (2001:6f8:12be:0:be05:43ff:fecc:c2a7) 7.786 ms 7.390 ms 7.069 ms 2 gw-3509.ham-01.de.sixxs.net (2001:6f8:900:db4::1) 41.146 ms 40.859 ms 40.558 ms 3 2001:6f8:862:1::c2e9:c729 (2001:6f8:862:1::c2e9:c729) 40.265 ms 39.960 ms 43.952 ms 4 vl2280.cr20.noham.de.easynet.net (2001:6f8:862:1::c2e9:c72d) 43.672 ms 47.698 ms 47.422 ms 5 2a00:74c0:0:1::c20f:9044 (2a00:74c0:0:1::c20f:9044) 47.127 ms 46.841 ms 50.841 ms 6 2003:0:1401:8001::2 (2003:0:1401:8001::2) 59.246 ms 47.039 ms 51.027 ms 7 2003:0:1401:8001::1 (2003:0:1401:8001::1) 55.057 ms 51.033 ms 50.665 ms 8 2003:0:1302:403::1 (2003:0:1302:403::1) 54.686 ms 54.425 ms 58.544 ms 9 2003:0:1302:403::2 (2003:0:1302:403::2) 56.334 ms 55.997 ms 55.716 ms 10 2003:51:6012::2 (2003:51:6012::2) 55.426 ms 55.135 ms 59.147 ms 11 * * * 12 * * * 13 * * * 14 * * * 15 * * * 16 *^C pi@jw-pi01 ~ $ sudo traceroute -6 -I mail.webertest.net traceroute to mail.webertest.net (2003:51:6012:110::15), 30 hops max, 80 byte packets 1 fritz.box (2001:6f8:12be:0:be05:43ff:fecc:c2a7) 6.574 ms 6.286 ms 10.484 ms 2 gw-3509.ham-01.de.sixxs.net (2001:6f8:900:db4::1) 39.192 ms 39.051 ms 38.896 ms 3 2001:6f8:862:1::c2e9:c729 (2001:6f8:862:1::c2e9:c729) 43.012 ms 42.934 ms 42.722 ms 4 vl2280.cr20.noham.de.easynet.net (2001:6f8:862:1::c2e9:c72d) 46.093 ms 45.907 ms 45.795 ms 5 2a00:74c0:0:1::c20f:9044 (2a00:74c0:0:1::c20f:9044) 50.001 ms 49.797 ms 53.961 ms 6 2003:0:1401:8001::2 (2003:0:1401:8001::2) 58.300 ms 55.230 ms 54.268 ms 7 2003:0:1401:8001::1 (2003:0:1401:8001::1) 67.409 ms 54.453 ms 53.445 ms 8 2003:0:1302:403::1 (2003:0:1302:403::1) 52.300 ms 54.891 ms 53.880 ms 9 2003:0:1302:403::2 (2003:0:1302:403::2) 53.113 ms 53.960 ms 53.062 ms 10 2003:51:6012::2 (2003:51:6012::2) 56.301 ms 48.489 ms 51.752 ms 11 * * * 12 * * * 13 * * * 14 * * * 15 * * * 16 *^Cpi@jw-pi01 ~ $ pi@jw-pi01 ~ $ sudo traceroute -6 -T -p 25 mail.webertest.net traceroute to mail.webertest.net (2003:51:6012:110::15), 30 hops max, 80 byte packets 1 fritz.box (2001:6f8:12be:0:be05:43ff:fecc:c2a7) 6.692 ms 6.480 ms 6.227 ms 2 gw-3509.ham-01.de.sixxs.net (2001:6f8:900:db4::1) 39.477 ms 39.249 ms 43.354 ms 3 2001:6f8:862:1::c2e9:c729 (2001:6f8:862:1::c2e9:c729) 42.876 ms 42.594 ms 42.437 ms 4 vl2280.cr20.noham.de.easynet.net (2001:6f8:862:1::c2e9:c72d) 42.148 ms 41.881 ms 45.981 ms 5 2a00:74c0:0:1::c20f:9044 (2a00:74c0:0:1::c20f:9044) 45.783 ms 49.853 ms 49.633 ms 6 2003:0:1401:8001::2 (2003:0:1401:8001::2) 59.960 ms 48.660 ms 56.695 ms 7 2003:0:1401:8001::1 (2003:0:1401:8001::1) 55.346 ms 54.374 ms 53.006 ms 8 2003:0:1302:403::1 (2003:0:1302:403::1) 51.783 ms 55.417 ms 54.242 ms 9 2003:0:1302:403::2 (2003:0:1302:403::2) 57.247 ms 46.086 ms 49.205 ms 10 2003:51:6012::2 (2003:51:6012::2) 57.578 ms 91.604 ms 90.407 ms 11 2003:51:6012:100::2 (2003:51:6012:100::2) 110.802 ms 113.621 ms 121.861 ms 12 mail.webertest.net (2003:51:6012:110::15) 120.499 ms 137.617 ms 146.114 ms |
pcap and Wireshark
This is the pcap file that consists of a sample run via IPv6 and TCP Port 25:
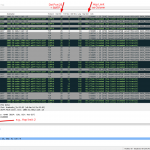
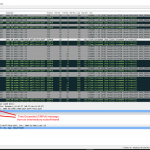
Otherwise here are two Wireshark screenshots that give an idea how TCP SYN packets to port 25 while incrementing the hop limit look alike:
Featured image: “Spuren von Tiefschnee-Geniessern” by Isabelle Pagano is licensed under CC BY-NC 2.0.


Hi, I am trying to use the cmd line to gain an understand of the physical hardware that the tracert requests are running through. Does tracert in Windows offer any further options in which a networks topologies could be layed out, beyond the simple, time-out length and IP address?
Hey Andrew. Huh, that’s probably hard. With Linux you can use the -A option to have the AS numbers displayed.
If you want to find out more information about the hardware you can run a port scan with OS detection such as Nmap is doing it: https://weberblog.net/my-nmap-command/
Don’t know if there are other, more reliable, techniques to do that. I suppose not.
Johannes