I am testing a lot with my own DNS servers as well as with third-party DNS implementations such as DNS proxies on firewalls, DNSSEC validation on resolvers, etc. While there are a number of free DNS online tools around the Internet I was lacking some DNS test names with certain properties or resource records. Hence I configured a couple of them on my own authoritative DNS servers and its zone weberdns.de.
For example, we encountered a bug on the Palo Alto DNS proxy that has not stored the TTL value correctly – hence some test names with different TTL values. Or we had some problems when a single DNS name has more than 15 IPv4/IPv6 addresses – hence some test names with lots of addresses. And many more:
Prenotes
- All names are within the weberdns.de zone. That is, always consider this domain as a suffix for all test names.
- My zone is DNSSEC signed with NSEC records. If you are interested in all of my names simply walk the zone by yourself. ;)
- Almost every test name has an AAAA as well as an A record. These are almost always from the “Address Prefix/Blocks Reserved for Documentation”, i.e., RFC 3849 for IPv6 and RFC 5737 for legacy IP.
- Note that all names and entries are fully correct due to the RFCs. There aren’t any false names or resource records such as wrong IP addresses, too-long TTLs, incorrect DNSSEC signatures, etc.
- This blogpost does NOT cover any possible DNS test case nor does it use any available RR. If you have any suggestions for more entries please write a comment below!
- Refer to the Domain Name System (DNS) Parameters from IANA or to this list of DNS record types on Wikipedia for any details about DNS resource records, etc.
Ok, let’s go:
TTL (Time to Live)
TTL values are between 0 and 2147483647 seconds, RFC 2181, section 8. My test entries:
- ttl-0s.weberdns.de with a TTL of 0 seconds
- ttl-1s.weberdns.de with a TTL of 1 second
- ttl-1m.weberdns.de with a TTL of 1 minute
- ttl-30d.weberdns.de with a TTL of 30 days
- ttl-52w.weberdns.de with a TTL of 52 weeks
- ttl-max.weberdns.de with a TTL of 2147483647 = 68 years (!)
When testing several DNS resolvers such as Google Public DNS, OpenDNS and some own servers with dnseval you can see the differences in the TTL handling. Some have a hard upper limit at 86400 while OpenDNS answers with a 0. Only my own Unbound DNS resolver answered correctly with 2147483647. (You have to scroll rightward to see the TTL column.)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
weberjoh@jw-nb15-lx:~/dnsdiag$ ./dnseval.py -f ../dns-servers ttl-max.weberdns.de server avg(ms) min(ms) max(ms) stddev(ms) lost(%) ttl flags ------------------------------------------------------------------------------------------------------------------ 194.25.0.68 18.907 5.001 67.823 21.441 %0 86400 QR -- -- RD RA AD -- 194.25.0.60 20.802 8.841 51.478 18.168 %0 86400 QR -- -- RD RA AD -- 2003:40:2000::53 5.339 4.736 6.628 0.652 %0 86400 QR -- -- RD RA AD -- 2003:56::53 8.431 8.131 8.880 0.210 %0 86400 QR -- -- RD RA AD -- 8.8.8.8 247.766 13.389 1064.080 429.064 %0 86399 QR -- -- RD RA AD -- 8.8.4.4 24.708 5.723 57.430 19.470 %0 86396 QR -- -- RD RA AD -- 2001:4860:4860::8888 125.638 13.279 1049.327 324.985 %0 86397 QR -- -- RD RA AD -- 2001:4860:4860::8844 118.542 13.660 1058.121 330.134 %0 86394 QR -- -- RD RA AD -- resolver1.opendns.com 12.836 7.117 17.994 4.044 %0 0 QR -- -- RD RA -- -- resolver2.opendns.com 9.049 6.377 14.403 3.004 %0 0 QR -- -- RD RA -- -- ns1-v4.weberdns.de 9.852 6.952 26.146 5.802 %0 2147483647 QR AA -- RD -- -- -- ns1-v6.weberdns.de 4.705 4.214 5.249 0.324 %0 2147483647 QR AA -- RD -- -- -- ns2.weberdns.de 9.181 8.979 9.918 0.268 %0 2147483647 QR AA -- RD -- -- -- ns3.weberdns.de 22.901 22.330 23.353 0.313 %0 2147483647 QR AA -- RD -- -- -- 192.168.110.1 3.941 2.800 11.848 2.782 %0 604800 QR -- -- -- -- -- -- 192.168.7.1 11.644 6.478 56.165 15.644 %0 86400 QR -- -- RD RA AD -- 192.168.7.5 15.164 11.962 41.730 9.341 %0 2147483647 QR -- -- RD RA AD -- |
Note that these TTL test names will possibly have wrong DNSSEC signatures some day since my KSK/ZSK key rollovers appear more often than every 68 years. ;) Some tools such as DNSViz point to that possible problem:
CNAME Loops/Array
Three different CNAME loops, one directly (loop->pool->), another over three records (cnamex->y->z), and an array with 5 consecutive CNAMEs:
|
1 2 3 4 5 6 7 8 9 10 11 |
loop IN CNAME pool pool IN CNAME loop cnamex IN CNAME cnamey cnamey IN CNAME cnamez cnamez IN CNAME cnamex cname1 IN CNAME cname2 cname2 IN CNAME cname3 cname3 IN CNAME cname4 cname4 IN CNAME cnamefinal cnamefinal IN AAAA 2001:db8:42:42:42:42:42:42 IN A 198.51.100.42 |
Using the standard Linux tool “host” this can look like:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
weberjoh@jw-nb12-lxold:~$ host loop.weberdns.de loop.weberdns.de is an alias for pool.weberdns.de. pool.weberdns.de is an alias for loop.weberdns.de. loop.weberdns.de is an alias for pool.weberdns.de. pool.weberdns.de is an alias for loop.weberdns.de. loop.weberdns.de is an alias for pool.weberdns.de. pool.weberdns.de is an alias for loop.weberdns.de. weberjoh@jw-nb12-lxold:~$ weberjoh@jw-nb12-lxold:~$ weberjoh@jw-nb12-lxold:~$ host cname1.weberdns.de cname1.weberdns.de is an alias for cname2.weberdns.de. cname2.weberdns.de is an alias for cname3.weberdns.de. cname3.weberdns.de is an alias for cname4.weberdns.de. cname4.weberdns.de is an alias for cnamefinal.weberdns.de. cnamefinal.weberdns.de has address 198.51.100.42 cnamefinal.weberdns.de has IPv6 address 2001:db8:42:42:42:42:42:42 |
As always, you can use DNSViz to get an idea of it:
Many IP Addresses per Name
I had a bug/feature on the Palo Alto FQDN objects in which I tested these names. It should be pretty clear how many addresses reside behind those names:
|
1 2 3 4 5 6 7 8 9 10 11 |
16a.weberdns.de 16aaaa.weberdns.de 16dual.weberdns.de 32a.weberdns.de 32aaaa.weberdns.de 32aaaa-long.weberdns.de 32dual.weberdns.de 32dual-long.weberdns.de 64a.weberdns.de 64aaaa.weberdns.de 64dual.weberdns.de |
In the same way here is a single name that has 10 different RRs with about 30 (!) values in summary (2x AAAA, 2x A, 2x TXT, RP, LOC, 8x SSHFP, APL, 8x CAA, NSEC, 9x RRSIG):
|
1 |
many-rrs.weberdns.de |
Querying this with “any” looks like that:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 |
weberjoh@vm19-lx2:~$ dig many-rrs.weberdns.de any ; <<>> DiG 9.10.3-P4-Ubuntu <<>> many-rrs.weberdns.de any ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 24646 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 35, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;many-rrs.weberdns.de. IN ANY ;; ANSWER SECTION: many-rrs.weberdns.de. 3599 IN CAA 0 issue "letsencrypt.org" many-rrs.weberdns.de. 3599 IN CAA 0 issue "pki.dfn.de" many-rrs.weberdns.de. 3599 IN CAA 0 issue "telesec.de" many-rrs.weberdns.de. 3599 IN CAA 0 issuewild "letsencrypt.org" many-rrs.weberdns.de. 3599 IN CAA 0 issuewild "telesec.de" many-rrs.weberdns.de. 3599 IN CAA 0 iodef "mailto:webmaster@webernetz.net" many-rrs.weberdns.de. 3599 IN CAA 0 issue "comodoca.com" many-rrs.weberdns.de. 3599 IN CAA 0 issuewild "pki.dfn.de" many-rrs.weberdns.de. 3599 IN RRSIG CAA 8 3 3600 20171103120853 20171004110853 32058 weberdns.de. b/afpIH6BQv2ZtTcK9k8PBO95/27RwIYguaSPLEo0in5OU2tjmID5kCR KjCPCCVqFpTnowA5bYAMrwQioP2kAF4eFrKUQNR566FpsE9yE2mrfSX8 duwPvQ9pZilAyzylBvD3kvcMRlDeuSUi9T+wncxkgnY4edN168/uYysg KaY= many-rrs.weberdns.de. 179 IN NSEC ns0.weberdns.de. A TXT RP AAAA LOC APL SSHFP RRSIG NSEC CAA many-rrs.weberdns.de. 179 IN RRSIG NSEC 8 3 180 20171103120853 20171004110853 32058 weberdns.de. duHtXnQchbeH7JxhVyH6xMdDxUbMfpScmb35LB7zm73CCk60uyiv5Gei FqaVnuvmY9v9v+vrSyW1cSsEbvMkdHpQ8Z9pMSq1kgLe7ZZ5KfSZRK0+ 6m8CJdwtWWzwHL9nS1DaqCVn3Qw5UA65Crg8Rt5/joI7r0TJy96nQZgD XKo= many-rrs.weberdns.de. 3599 IN RRSIG A 8 3 3600 20171103120853 20171004110853 32058 weberdns.de. MuvounkMQHEGnRnQNU2NU9iatZo3k98YECp5tpVwczkqKHCFmeRp+o6k Wn7mOZ4eG4MGa46AieiXxsL9uS/0NkqpeYsbmQpSSG14XWSUJVsy8T5/ AFJvXr3gXgFCJs7AAEH/uUtPZO4qOiOV0XmPPsN/fNFPkk4/VOvF69bB s4M= many-rrs.weberdns.de. 3599 IN RRSIG TXT 8 3 3600 20171103120449 20171004110449 32058 weberdns.de. ZbaaAZhAJpGH8OlFr7X56/VatQxTmF8KS40COxHUtjihU5D/MY2NdSJB T9MBlOqq++zvP9lozJz6z4naDDmQ0/55O/m5UQl7tnMZ18Anl/iLe3k4 Ph94SkJ8F4fbmFW7ecitqBwcMFhxPsluSH3VLxu2t4QZtRYxuzqkBUIj RGM= many-rrs.weberdns.de. 3599 IN RRSIG RP 8 3 3600 20171103120449 20171004110449 32058 weberdns.de. yfc9pKt7kLioTV81oNmM/NTsOcNcCXYNSClUCfmJL4/HkCJZcDWJXYxI Z2Gsvyn9HFNWvtQhUGkyyAtDRmixrE9BKkeE/VNMSegaBwBcTeNkloOw Ig/eX06+CfsIAnSq9u/XYGjTiWt/CA7RxDKiURcvgNZyh2v5IuGU1APV VdM= many-rrs.weberdns.de. 3599 IN RRSIG AAAA 8 3 3600 20171103122214 20171004112214 32058 weberdns.de. U/kfxtVzYcmwqUstvDIx9yry89+N2bHA0y681YRM+4kGKBWjdyhPSBoJ mVK5n41xtaUQ1SPF2tiM1fbPIe55inQRuBQndkVhSXloPQPVpdH6I5xP NqlDWSVyQL1eiPCIe6Nr15te2THDFHIOaCYK7m5HJ1W47dVZ7jYpWz7V mbE= many-rrs.weberdns.de. 3599 IN RRSIG LOC 8 3 3600 20171103120449 20171004110449 32058 weberdns.de. rv4GJe9YGEwSYc3ZDdrgVWl2Zjh09eD0D1Y4tAVXDLoMsj2svv6BkRWg cGzkdlrgXfo4N/3oHoXnRu5goB1HXHep/MVcRyOiBeMhLqFQTGC+PVum 5j6jkIWajT7Yn94qt6tUzi+J+w2X0OR5FeprqNc+SLLDD6Llty1LtIXE W6I= many-rrs.weberdns.de. 3599 IN RRSIG APL 8 3 3600 20171103120449 20171004110449 32058 weberdns.de. DNmHL1Wre7Pp0aaRevRAfk8/kjjM4c0k+wFC5D7nQ5pBvknRmDk0Kutk MZ8X0ezZ6eY2ohTs8bq+rMlD25DBtPku7sj9cazrehMY4gtHMQOx3GVh onSPVL+WdBLtFJM7YEK33xuZZt5K/gkjj6zK8jMypu6blKDO/bfQ2rGh xxc= many-rrs.weberdns.de. 3599 IN RRSIG SSHFP 8 3 3600 20171103120449 20171004110449 32058 weberdns.de. QlCHbWXLx/L4b2u2Eo5jZUkRY+Llw+dGHe5Oz0p2IFzAnuHG1YQtVjbb v/jdW4U1wh2kYOr3/NfN9OuFpO56ytsNd+PGKJSHw8ONalhdYpGVpXnz sRoDc7xZMnv/R6QOxR7Wxj7gFeQIisrpkGcT1O6kLkM58hEtFy2Nv8uX dHA= many-rrs.weberdns.de. 3599 IN SSHFP 4 1 E9D762CA6B63931A92DE1C697DE32576B8F688F7 many-rrs.weberdns.de. 3599 IN SSHFP 4 2 94922EC5B5DB59E481AD9D92AF3D8A510B1A646C14A49632439B587B 16F8F7BE many-rrs.weberdns.de. 3599 IN SSHFP 1 2 4900A938D3D66780282BD11ED0B1ADD185B840A5E53593C7E3B61F05 B6380957 many-rrs.weberdns.de. 3599 IN SSHFP 1 1 3EEFEA71CA65FB5D8F45F4330B7268B4A41D14A5 many-rrs.weberdns.de. 3599 IN SSHFP 3 2 F2B4EE8F420F05562B23497D410EEA8DFAE6017DBA8251C263368A57 94B5D743 many-rrs.weberdns.de. 3599 IN SSHFP 2 2 23FB1547769A831B4421300E69BDFFCDD16500100A3CD5B9CED7C689 DEBB09E7 many-rrs.weberdns.de. 3599 IN SSHFP 3 1 1F2D63725710D15C14FD88ABF4EC9CAB0554C633 many-rrs.weberdns.de. 3599 IN SSHFP 2 1 5DEDB27F448E1F5CBC6773BBC6C50E51DFC1E18D many-rrs.weberdns.de. 3599 IN APL 2:2001:db8::/32 1:192.0.2.0/24 1:198.51.100.0/24 1:203.0.113.0/24 many-rrs.weberdns.de. 3599 IN LOC 50 15 20.300 N 8 38 47.700 E 186.00m 20m 50m 10m many-rrs.weberdns.de. 3599 IN AAAA 2001:db8::43 many-rrs.weberdns.de. 3599 IN AAAA 2001:db8::42 many-rrs.weberdns.de. 3599 IN RP johannes.webernetz.net. johannes.weberdns.de. many-rrs.weberdns.de. 3599 IN TXT "This is a single DNS name with many different RRs." many-rrs.weberdns.de. 3599 IN TXT "For example it has two TXT records and eight SSHFP records." many-rrs.weberdns.de. 3599 IN A 192.0.2.43 many-rrs.weberdns.de. 3599 IN A 192.0.2.42 ;; Query time: 32 msec ;; SERVER: 8.8.4.4#53(8.8.4.4) ;; WHEN: Wed Oct 04 14:22:19 CEST 2017 ;; MSG SIZE rcvd: 2563 |
Long Names and Subdomains
The longest single name/label can be 63 chars/octets long (RFC 1035, section 2.3.4):
|
1 |
abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyz1234567890.weberdns.de |
While the longest name at all can be 253 chars/octets, separated in different labels that are 63 chars long (good explanation here: “If you sit down and do the math, you’ll see that the the readable maximum length of an ASCII DNS name is 253 characters.”):
|
1 |
abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyz1234567890.abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyz1234567890.abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyz1234567890.abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyz.weberdns.de |
If you only want to test a few subdomains (without these long labels):
|
1 2 3 4 5 6 7 8 |
sub1.weberdns.de sub2.sub1.weberdns.de sub3.sub2.sub1.weberdns.de sub4.sub3.sub2.sub1.weberdns.de sub5.sub4.sub3.sub2.sub1.weberdns.de sub6.sub5.sub4.sub3.sub2.sub1.weberdns.de sub7.sub6.sub5.sub4.sub3.sub2.sub1.weberdns.de sub8.sub7.sub6.sub5.sub4.sub3.sub2.sub1.weberdns.de |
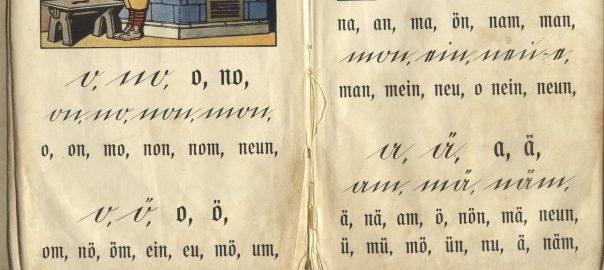
Umlaute

In Germany we do not have only 26 characters but 30. ;) Following are a few internationalized domain names (IDN) from a couple of european character sets. There are many IDN Web Converter tools out there to generate them. A test case for many DNS related servers is the correct transformation into the ASCII text presentation of these names. (Almost all of the following names have a TXT record that give a short description about its meaning. Just for fun.)
|
1 2 3 4 5 6 7 8 9 10 11 |
übergrößenträger.weberdns.de heizölrückstoßabdämpfung.weberdns.de seïr.weberdns.de fanø.weberdns.de fünf.weberdns.de désirée.weberdns.de hår.weberdns.de yoğurt.weberdns.de áàăâåäãąąāæćĉčċçďđéèĕêěëėęēğĝġģ.weberdns.de íìĭîïĩįīıĵķĺľļłńňñņŋóòŏôöőõøōœĸ.weberdns.de ŕřŗśŝšşßťţŧúùŭûůüűũųūŵýŷÿźžżðþ.weberdns.de |
Note that not all DNS lookup tools provide the transformation into IDNs. For example, nslookup won’t:
|
1 2 3 4 5 6 7 8 9 10 11 |
C:\Users\weberjo>nslookup übergrößenträger.weberdns.de DNS request timed out. timeout was 2 seconds. Server: UnKnown Address: 172.20.10.1 DNS request timed out. timeout was 2 seconds. DNS request timed out. timeout was 2 seconds. *** übergrößenträger.weberdns.de wurde von UnKnown nicht gefunden: Non-existent domain. |
While it will work if you’re asking after the transformation directly:
|
1 2 3 4 5 6 7 8 |
C:\Users\weberjo>nslookup xn--bergrssentrger-gib5zmd.weberdns.de Server: UnKnown Address: 172.20.10.1 Nicht autorisierende Antwort: Name: xn--bergrssentrger-gib5zmd.weberdns.de Addresses: 2001:db8::1 198.51.100.1 |
Other RRs
A few well-known and not-so-well-known RRs:
- AAAA: aaaa.weberdns.de
- A: a.weberdns.de
- CNAME: cname.weberdns.de
- TXT: txt.weberdns.de
- SRV (Location of Services, RFC 2782): _sip._tcp.weberdns.de
- APL (Lists of Address Prefixes, RFC 3123): ip-documentation.weberdns.de
- RP (Responsible Person, RFC 1183): host-dane-self.weberdns.de
- HINFO (host information, RFC 883, RFC 1700): host-dnssec.weberdns.de
The zone itself weberdns.de can be queried for the following records:
- SOA
- NS
- MX
- CAA (DNS Certification Authority Authorization, RFC 6844)
- LOC (Location Information, RFC 1876)
Example with dig:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
weberjoh@jw-nb12-lxold:~$ dig weberdns.de soa ; <<>> DiG 9.10.3-P4-Ubuntu <<>> weberdns.de soa ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 1972 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 5 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;weberdns.de. IN SOA ;; ANSWER SECTION: weberdns.de. 3600 IN SOA ns0.weberdns.de. webmaster.weberdns.de. 2017092512 3600 900 2419200 180 ;; Query time: 18 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Mon Sep 25 20:55:32 CEST 2017 ;; MSG SIZE rcvd: 216 |
DNSSEC related RRs
The following DNSSEC related RRs can be queried through the zone as well:
- DNSKEY at weberdns.de (shows at least one “257” KSK and one “256” ZSK)
- DS for weberdns.de (this RR is NOT stored at my zone itself but on the parent zone)
- RRSIG for any name, e.g. for a.weberdns.de which shows the RRSIG for its “A” and “NSEC” record
- NSEC for any name, e.g. for a weberdns.de which points to aaaa.weberdns.de
A demo run of these four queries is listed below:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 |
weberjoh@jw-nb15-lx:~$ dig weberdns.de dnskey ; <<>> DiG 9.10.3-P4-Ubuntu <<>> weberdns.de dnskey ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17837 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 3, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;weberdns.de. IN DNSKEY ;; ANSWER SECTION: weberdns.de. 975 IN DNSKEY 257 3 8 AwEAAbBpiuX423e8HACUAvARMzUH+stqMAFq0jmthfA7FQc8d5sqMfZc K0vcg4QFIotAVIh8AfATggHP7tIy6rVuKqCnvF4LFan4ONNZ7c3WhLMi HB80F4M85NmRMMh/ssb32X10Th+iN3g2vPJtvP+rxoeRVT5XyNwbDB+A UCZgsElwwRmgB+UPQPLU1pZg9bOKW07ejdtayplItPqiuLQ5eRp8OWeb 92AtSpAORp8g4phc+ctvoH9a79lLCszTXiiJgaW38iLwD5rZHvqmKL6m Sq/qEgxaQHkphinyfYJ7YzH+kbmOn7WXCgfbjSrVYhiCXeK+NKGgbUwJ lwbHVfdYLVM= weberdns.de. 975 IN DNSKEY 256 3 8 AwEAAdx+50fsj7Sxy2DvKiSIdo5YKl/REUJxgson+6O2aXba9Kaj8Eow wmc/9gOacvCrQyzr3TY2b1wdP0Gg0VeHYoa0A1LxWa9dy2Ts14yixcZ5 KFYzubkz+doteFa3BFeJoanQLLaDvB1Tx1GNz2XuuNvznZ4/ptQuqCQU PcvSYENn weberdns.de. 975 IN DNSKEY 257 3 8 AwEAAdQXI+UfqnGbHdwJtBBStf0CM8Q8nXcriaOysrpGEDNkM//amUBD 2YMWQ3g+htca6tmzfDJMM5D0gOk5d4IdEmdywkcH+0rGLjNiNEPFnZUp wb6XsYD+ZI/WEuSlp+KCEV8vwELq7VltABrFT+9Rz5CEvokTxonzQrvn fclVHaGwO7cglgALsFqJCqBpvDZvEr2Z6dSepjDnFC9BPS6V8PGSNwAY EtzDp/lrQojkCj28xHj2OCjpr0dIQjdjGFJTHIlc9cYTAHjdPDsC8Eqf s5HcL3ruU6cbqjTn+5Lm4RdXpOWVgemVvIGDnUN+v+Tma/WgtQk7U3sa izNJ3epCv3s= ;; Query time: 1 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Mon Sep 25 21:03:47 CEST 2017 ;; MSG SIZE rcvd: 740 weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ dig weberdns.de ds ; <<>> DiG 9.10.3-P4-Ubuntu <<>> weberdns.de ds ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 10281 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;weberdns.de. IN DS ;; ANSWER SECTION: weberdns.de. 69407 IN DS 63202 8 2 2F9112FF344BCDF9C6F9A7548F04184AAE73458C7150DE8FFFA3B7D9 893C5EEE ;; Query time: 1 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Mon Sep 25 21:03:52 CEST 2017 ;; MSG SIZE rcvd: 88 weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ dig a.weberdns.de rrsig ; <<>> DiG 9.10.3-P4-Ubuntu <<>> a.weberdns.de rrsig ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 61163 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 2, AUTHORITY: 3, ADDITIONAL: 5 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;a.weberdns.de. IN RRSIG ;; ANSWER SECTION: a.weberdns.de. 3509 IN RRSIG A 8 3 3600 20171025185923 20170925175923 32058 weberdns.de. 0RGSdHTuaOYxpxh738xT3zW9w2qoaq6y3EsT1C5D8C8GyKuITqkVxVmZ IdgKq8x0SvEIlODsFVi94hbfVt2zYcfFU5IcdTCEC/AxCNzjbkezigcg nJwjSixu0olpafTfbSVhvjPK8SIpX+FYRJzKW1fwrcbLp4liMAypne7J 4Yg= a.weberdns.de. 66 IN RRSIG NSEC 8 3 180 20171025185923 20170925175923 32058 weberdns.de. ttb3eukAdFOaBfO5fc35p7DSweCJaeOEI7SIAX4NB7oFoMmkrn+C0CTv YERXNXLgueW2XNZFP8oN+B2uWJcq2EmiWTI9iEuC6hE4NYuWGoyTIojf 08GsXMcz/Di2s6zIokKtNjhRW5yUt/7HV9abWH9ty3ET5fJkpKJZTIfr 8Ms= ;; Query time: 2 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Mon Sep 25 21:04:02 CEST 2017 ;; MSG SIZE rcvd: 514 weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ dig a.weberdns.de nsec ; <<>> DiG 9.10.3-P4-Ubuntu <<>> a.weberdns.de nsec ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 54026 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 5 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;a.weberdns.de. IN NSEC ;; ANSWER SECTION: a.weberdns.de. 62 IN NSEC aaaa.weberdns.de. A RRSIG NSEC ;; Query time: 2 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Mon Sep 25 21:04:06 CEST 2017 ;; MSG SIZE rcvd: 210 |
Note that I don’t have any NSEC3 resource records in this zone since it’s signed with NSEC and not NSEC3. However, I have another zone called sshfp.net which uses NSEC3. Hence you can query the following RRs there:
- NSEC3PARAM on sshfp.net
- NSEC3 on any non-existent domain name such as foobar.sshfp.net. Note that the NSEC3 RR cannot (!) be queried directly. It only shows up when requesting some non-existent names.
Demo run:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 |
weberjoh@jw-nb15-lx:~$ dig sshfp.net nsec3param ; <<>> DiG 9.10.3-P4-Ubuntu <<>> sshfp.net nsec3param ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 13045 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 5 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;sshfp.net. IN NSEC3PARAM ;; ANSWER SECTION: sshfp.net. 0 IN NSEC3PARAM 1 0 20 80637D8AF055B5EECA2A621EDAAA3C5E ;; Query time: 5 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Mon Sep 25 21:20:16 CEST 2017 ;; MSG SIZE rcvd: 212 weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ weberjoh@jw-nb15-lx:~$ dig foobar.sshfp.net +dnssec ; <<>> DiG 9.10.3-P4-Ubuntu <<>> foobar.sshfp.net +dnssec ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NXDOMAIN, id: 37087 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 0, AUTHORITY: 6, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags: do; udp: 4096 ;; QUESTION SECTION: ;foobar.sshfp.net. IN A ;; AUTHORITY SECTION: sshfp.net. 161 IN SOA ns0.weberdns.de. webmaster.weberdns.de. 2017091805 3600 900 2419200 180 sshfp.net. 161 IN RRSIG SOA 10 2 86400 20171025050529 20170925040529 31055 sshfp.net. evNnTfm6kDrVG56/zK2WMAeinAHfdI7huAE8J1Dmmqib1slLVIVB4Pt9 YV7SsjbH6+j5lpxejZD0RWS1ryojFF8fCIzRZQXOhwSNTkn4EGJrCnxz nmRBHyoWGsO4rSoFq+XWNbOEoi+sqV7AaAwjO01bIu8Hody+oNg8b/+O 5qk+bm+2v2In37/3aVKp7MZzEay1EkwKAT009E0KfNn7oN9DFprQPu+R oAyOLaL1mOcAyRENdtDpcswriE1TKxZb4k67xjhacgf+TehKrk9Ly2hL 2MW7Tp9JqHQ0JJkASBcWWsuwwbDsGgCn5g+bHFbRPDOC85wPWlugWCgI Ro3AhA== 7M53TDGQJNT9A6I2QTRPO7OL0Q2Q06A7.sshfp.net. 161 IN RRSIG NSEC3 10 3 180 20171018075611 20170918065611 31055 sshfp.net. VeTCTuDBbu1geLnAv12odLFh/jbpYU33ybjBJ/i6s9C6lNchz/75sTo9 cP71aMzeEqtFeYMAplf8mB/P4PUDdur6Wh6yxlw/C5miXNujbJ+/Xunh +QSUouC8RG0kK48I5LhM7uid3Sl5nA5Cd0QEou/QkmhFHOzQ0DH4DGfK dRP93qc1i0X+W7JDwmD9Zhc54l4yKSs1PoMyg7qUVPb+8nzILFMg2O6S KQWvx6RLOf3WkSbbPNGAP7pk0+mXh45aVyVS8MCXdlV2jfxf/PqLNI0v 3ISKKHRGkYcpAOuyWcssAUnMUjYWLIX7tmoWcUCbirR5FF0b65dYEULo jBG72w== 7M53TDGQJNT9A6I2QTRPO7OL0Q2Q06A7.sshfp.net. 161 IN NSEC3 1 0 20 80637D8AF055B5EECA2A621EDAAA3C5E SO7GF8PJF86DIQR1AHF14H4MVBHJAIU6 CNAME RRSIG VLQ247QI8P1TT3A8CGMD7GLFNDTIGSDU.sshfp.net. 161 IN RRSIG NSEC3 10 3 180 20171018075611 20170918065611 31055 sshfp.net. YTjdsxOZhgIh6X9H0a3MYsyW3G1PV4IfjoJ/ksBbe6ZgPiYRK25xzutb aPSCN6WqWkS9XtubHSBDOtBl62tUJjEf+HwTykkYsyUvjVz1NSSInPuN OyMLqVolHy146YPw62iZKTVptUal8kdWvCCkB8tC/hnDEw8YbOG1aYUW lyMZZ51032bqrrFG0SX1/6fOAFfxhZgTT4rKfuJHiai8jnLlZjGHsxhU q3HYoaMz6r2pome33oxAU4QS6w9DoR+mD8htcyLst+mghG7NYRQju2Wh uNk/u2y2KKdeOMgaMctGnq/6rpt/wwkOAmSYBougBnkygN/E9AhPjvWq L3WS5A== VLQ247QI8P1TT3A8CGMD7GLFNDTIGSDU.sshfp.net. 161 IN NSEC3 1 0 20 80637D8AF055B5EECA2A621EDAAA3C5E 7M53TDGQJNT9A6I2QTRPO7OL0Q2Q06A7 NS SOA MX TXT RRSIG DNSKEY NSEC3PARAM ;; Query time: 7 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Mon Sep 25 21:20:20 CEST 2017 ;; MSG SIZE rcvd: 1188 |
With a working DNSSEC environment you can use the following additional DNS RRs:

- TLSA (DNS-Based Authentication of Named Entities, RFC 6698):
_25._tcp.mail.weberdns.de - SSHFP (SSH Key Fingerprints, RFC 4255):
ns1.weberdns.de - OPENPGPKEY (DANE for OpenPGP, RFC 7929): I have a 2048 bit OpenPGP key for the test mailaddress johannes@weberdns.de (which is NOT my actual mailaddress). Since OPENPGPKEY uses the first 28 octets from the SHA-256 hashed local-part of the mailadress you can query the following name for its OPENPGPKEY resource record: 1d4b41c9db9172e5f151e4a5fe3c57ca3f98b8e6ba807450b10d1897._openpgpkey.weberdns.de. For a 4096 bit OpenPGP public key you can use the following mail address ludwig@weberdns.de which has a DNS name of: faae1b97e57e3e121216948b8dda2a429ea72d6dd81c164f227dc6a1._openpgpkey.weberdns.de
Demo:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 |
weberjoh@nb15-lx:~$ dig _25._tcp.mail.weberdns.de tlsa ; <<>> DiG 9.10.3-P4-Ubuntu <<>> _25._tcp.mail.weberdns.de tlsa ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 20375 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 5 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;_25._tcp.mail.weberdns.de. IN TLSA ;; ANSWER SECTION: _25._tcp.mail.weberdns.de. 3600 IN TLSA 3 0 1 AE822A14FD5E56C213EEEB5D6755556980CAF4C3F2531C1EC8ECA307 6F9B7E68 ;; Query time: 4 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Thu Oct 05 10:50:40 CEST 2017 ;; MSG SIZE rcvd: 231 weberjoh@nb15-lx:~$ weberjoh@nb15-lx:~$ weberjoh@nb15-lx:~$ dig ns1.weberdns.de sshfp ; <<>> DiG 9.10.3-P4-Ubuntu <<>> ns1.weberdns.de sshfp ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 63551 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 6, AUTHORITY: 3, ADDITIONAL: 5 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;ns1.weberdns.de. IN SSHFP ;; ANSWER SECTION: ns1.weberdns.de. 3600 IN SSHFP 3 1 874309C8A92FA68F247E7E619DAF17E0D2425397 ns1.weberdns.de. 3600 IN SSHFP 2 2 75A0F3538780A051CACB3C1511A7647D1730348950E21F627AFA7637 D9691713 ns1.weberdns.de. 3600 IN SSHFP 3 2 57052FF290DFEF352037A6A67D8448D926E9EA456DA84164E6E88197 59D9550B ns1.weberdns.de. 3600 IN SSHFP 1 2 6D67423D7C36C22E6910B503B96026FDDFBF6D19A31CB3AC11CF1ECE 8A0087E9 ns1.weberdns.de. 3600 IN SSHFP 1 1 758B951FF36B30AB8F6D05B3694A041559DD9D68 ns1.weberdns.de. 3600 IN SSHFP 2 1 F5D7944A1545C29F03AD7042F1D0929D38E5F616 ;; Query time: 5 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Thu Oct 05 10:51:08 CEST 2017 ;; MSG SIZE rcvd: 410 weberjoh@nb15-lx:~$ weberjoh@nb15-lx:~$ weberjoh@nb15-lx:~$ dig 1d4b41c9db9172e5f151e4a5fe3c57ca3f98b8e6ba807450b10d1897._openpgpkey.weberdns.de openpgpkey +multi ; <<>> DiG 9.10.3-P4-Ubuntu <<>> 1d4b41c9db9172e5f151e4a5fe3c57ca3f98b8e6ba807450b10d1897._openpgpkey.weberdns.de openpgpkey +multi ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 41879 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 5 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;1d4b41c9db9172e5f151e4a5fe3c57ca3f98b8e6ba807450b10d1897._openpgpkey.weberdns.de. IN OPENPGPKEY ;; ANSWER SECTION: 1d4b41c9db9172e5f151e4a5fe3c57ca3f98b8e6ba807450b10d1897._openpgpkey.weberdns.de. 3579 IN OPENPGPKEY ( mQENBFnVAMgBCADWXo3I9Vig02zCR8WzGVN4FUrexZh9 OdVSjOeSSmXPH6V5+sWRfgSvtUp77IWQtZU810EI4Ggc Ezg30SEdLBSYZAt/lRWSpcQWnql4LvPgoMqU+/+WUxFd nbIDGCMEwWzF2NtQwl4r/ot/q5SHoaA4AGtDarjA1pbT Bxza/xh6VRQLl5vhWRXKslh/Tm4NEBD16Z9gZ1CQ7YlA U5Mg5Io4ghOnxWZCGJHV5BVQTrzzozyILny3e48dIwXJ KgcFt/DhE+L9JTrO4cYtkG49k7a5biMiYhKhLK3nvi5d iyPyHYQfUaD5jO5Rfcgwk7L4LFinVmNllqL1mgoxadpg PE8xABEBAAG0MUpvaGFubmVzIFdlYmVyIChPTkxZLVRF U1QpIDxqb2hhbm5lc0B3ZWJlcmRucy5kZT6JATgEEwEC ACIFAlnVAMgCGwMGCwkIBwMCBhUIAgkKCwQWAgMBAh4B AheAAAoJEOvytPeP0jpogccH/1IQNza/JPiQRFLWwzz1 mxOSgRgubkOw+XgXAtvIGHQOF6/ZadQ8rNrMb3D+dS4b TkwpFemY59Bm3n12Ve2Wv2AdN8nK1KLClA9cP8380CT5 3+zygV+mGfoRBLRO0i4QmW3mI6yg7T2E+U20j/i9IT1K ATg4oIIgLn2bSpxRtuSp6aJ2q91Y/lne7Af7KbKq/Mir EDeSPrjMYxK9D74EABLs4Ab4Rebg3sUga037yTOCYDpR v2xkyARoXMWYlRqME/in7aBtfo/fduJGqu2RlND4inQm V75V+s4/x9u+7UlyFIMbWX2rtdWHsO/t4sCP1hhTZxz7 kvK71ZqLj9hVjdW5AQ0EWdUAyAEIAKxTR0AcpiDm4r4Z t/qGD9P9jasNR0qkoHjr9tmkaW34Lx7wNTDbSYQwn+WF zoT1rxbpge+IpjMn5KabHc0vh13vO1zdxvc0LSydhjMI 1Gfey+rsQxhT4p5TbvKpsWiNykSNryl1LRgRvcWMnxvY fxdyqIF23+3pgMipXlfJHX4SoAuPn4Bra84y0ziljrpt Wf4U78+QonX9dwwZ/SCrSPfQrGwpQcHSbbxZvxmgxewe HuAEhUGVuwkFsNBSk4NSi+7Y1p0/oD7tEM17WjnONuoG CFh1anTS7+LE0f3Mp0A74GeJvnkgdnPHJwcZpBf5Jf1/ 6Nw/tJpYiP9vFu1nF9EAEQEAAYkBHwQYAQIACQUCWdUA yAIbDAAKCRDr8rT3j9I6aDZrB/9j2sgCohhDBr/Yzxlg 3OmRwnvJlHjs//57XV99ssWAg142HxMQt87s/AXpIuKH tupEAClN/knrmKubO3JUkoi3zCDkFkSgrH2Mos75KQbs pUtmzwVeGiYSNqyGpEzh5UWYuigYx1/a5pf3EhXCVVyb IJwxDEo6sKZwYe6CRe5fQpY6eqZNKjkl4xDogTMpsrty 3snjZHOsQYlTlFWFsm1KA43Mnaj7Pfn35+8bBeNSgiS8 R+ELf66Ymcl9YHWHHTXjs+DvsrimYbs1GXOyuu3tHfKl ZH19ZevXbycpp4UFWsOkSxsb3CZRnPxuz+NjZrOk3UNI 6RxlaeuAQOBEow50 ) ;; Query time: 2 msec ;; SERVER: 2003:de:2016:120::a08:53#53(2003:de:2016:120::a08:53) ;; WHEN: Thu Oct 05 10:51:48 CEST 2017 ;; MSG SIZE rcvd: 1451 |
FIN.
Am I missing something? Please write a comment below!
Links
- IANA: Domain Name System (DNS) Parameters
- Wikipedia: List of DNS record types
- Interesting security related article about Chrome and Firefox Phishing Attack Uses Domains Identical to Known Safe Sites
- DNS Propagation Checker: https://dnschecker.org/
- DNS Lookup Tool, DNSWatch: https://www.dnswatch.info/
Featured image: “Umlauts” by Nina Stössinger is licensed under CC BY-SA 2.0.




thanks for hosting this :)
the other reason for my coment is a problem i witnessed with Umlauten in computer names. In my homelab i use a PAN FW with DHCP server enabled.
one day, i had a dhcp client, which had Umlate in his computername. (don’t ask!)
At this time i couldn’t display the DHCP leases on this subnet in the GUI.
Over the CLI i saw special characters in my leases. :D