I got an interesting question through the comments section on my blog:
Quite a good questions. Let’s have a look:
Indeed the firewall never receives or sends packets directly to/from itself, but rather processes packets. (Ok, there are exceptions such as management access via ping, ssh, https to a data interface or IPsec traffic to the WAN interface or OSPF to an internal interface.)
However, all the “sent/received” values are based on the source -> destination connection aka client -> server. That is: for both, UDP and TCP, the client always starts the connection to the server. For TCP, the client sends the very first TCP SYN packet while for UDP the client simply sends the data immediately without a handshake. That is: The “sent/received” values are ALWAYS from the clients perspective! Just like in the direction of the policies itself.
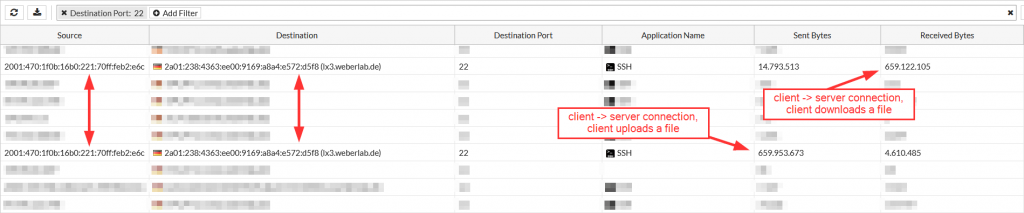
Let’s have a look at an example: An SSH connection is made from a client to a server. The IP address from the client is the source, while the IP address from the server is the destination. If this SSH connection is used by SCP in which the client uploads a 1 GB file to the server, this 1 GB is listed as “sent“. If in another session the same client downloads a 1 GB file from the server, the “source” and “destination” IP addresses are still the same (since the same client has started the session through the same security policy), while this 1 GB is counted as “received“.
This is what these two scenarios look like on a Palo Alto Networks firewall (with a ∼600 MB file, first uploaded by the client, second downloaded by the client):
Or on a Fortinet FortiGate:
Of course, when you’re looking at the sent/received values from the network interface cards (NIC) on the client or the server, the values correspond to the direction. If the client uploads a file, its own sent values increase while the received values do the same on the server, and vice versa.
Furthermore, everything that has been said here also applies to the count of packets, not only to the count of bytes.
God’s blessing!
Photo by Hello I’m Nik on Unsplash.



Thanks for pointing that out. To me this was obvious; personally I get confused by the same counter at switches ;-P