And one more IPsec VPN post, again between the Palo Alto Networks firewall and a Fortinet FortiGate, again over IPv6 but this time with IKEv2. It was no problem at all to change from IKEv1 to IKEv2 for this already configured VPN connection between the two different firewall vendors. Hence I am only showing the differences within the configuration and some listings from common CLI outputs for both firewalls.
I am using exactly the same lab environment as in my last blogpost. Please refer to it for any details about the IP addressing scheme, etc. I am still running at PAN-OS version 8.0.3 and FortiOS v5.4.5, build1138.
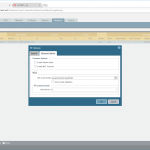
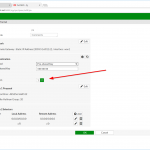
To use IKEv2 for an IPsec VPN tunnel you must only change the phase 1 settings on both endpoints, such as shown in the following screenshots for the Palo Alto Networks as well as for the Fortinet firewall:
For the sake of completeness here is my Fortinet configuration in CLI mode. It also shows the two default routes as well as the two VPN routes:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 |
config vpn ipsec phase1-interface edit "pa" set interface "wan1" set ip-version 6 set ike-version 2 set keylife 28800 set peertype any set proposal aes256-sha512 set dhgrp 20 set nattraversal disable set remote-gw6 2003:51:6012::2 set psksecret ENC noYsWA0We7N6wcl4NKacI01p6Uiuua+HJVYMn5f0tUpJrqCt56xLETuX98ra5Tskd9GWy2p90jJI5RsCdH7BoMcddK4lGZSXn3WuHw456vkt0N3gsb6xGiH0/tj17Pfem5LpcBRDlufFvaKpfUcFp0TFnJR783kKwpCg5IZOWjFk8UR53XkyOsvFuLN+m/C2QY7aNA== next end config vpn ipsec phase2-interface edit "pa" set phase1name "pa" set proposal aes256-sha512 set dhgrp 20 set auto-negotiate enable set keylifeseconds 3600 next edit "pa6" set phase1name "pa" set proposal aes256-sha512 set dhgrp 20 set auto-negotiate enable set src-addr-type subnet6 set dst-addr-type subnet6 set keylifeseconds 3600 next end config router static edit 1 set gateway 80.154.108.225 set device "wan1" next edit 2 set dst 192.168.110.0 255.255.255.0 set device "pa" next end config router static6 edit 1 set gateway 2003:51:6012::1 set device "wan1" next edit 2 set dst 2003:51:6012:110::/64 set device "pa" next end |
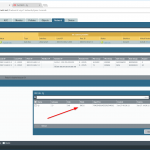
After committing the changes and some initial traffic the VPN tunnel comes up. The Palo GUI shows the “IKEv2” mode while the Fortinet does not list the used mode:
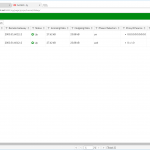
The CLI outputs from both firewalls changed a bit compared to the IKEv1 output. For example, the Palo lists the “Child SAs” in the ike-sa detail part and the “traffic selectors” in the vpn flow. Formerly they were called “proxy-id”.
Here are some outputs from the Palo Alto:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 |
weberjoh@pa> show vpn ike-sa detail gateway fg IKE Gateway fg, ID 23 2003:51:6012::2 => 2003:51:6012::4 Current time: Jun.27 09:43:53 IKE SA: SPI: 257D196A85066784:4175CD992C3C06F4 Init State: Established SN: 6 Authentication: PSK Proposal: AES256-CBC/SHA512/DH20 ID local: ipaddr:2003:51:6012::2 remote: ipaddr:2003:51:6012::4 ID_i: : ID_r: : NAT: Not detected Message ID: rx 9, tx 2352 Liveness check: sending informational packet after idle 5 seconds Created: Jun.27 06:28:21, 3 hours 15 minutes 32 seconds ago Expires: Jun.27 14:28:21, rekey in 3 hours 44 minutes 15 seconds (25187 sec) Child SA 18508: Tunnel 32 fg:fg Type: ESP Resp State: Mature Message ID: 00000006 Parent SN: 6 SPI: DDB5F90D : 3D713140 <= ESP: 3D71313E Algorithm: AES256/SHA512/DH20 TS local: Proto:any, 0.0.0.0-255.255.255.255, Ports:any TS remote: Proto:any, 0.0.0.0-255.255.255.255, Ports:any Created: Jun.27 08:50:35, 53 minutes 18 seconds ago Expires: Jun.27 09:50:35 Child SA 18692: Tunnel 33 fg:fg6 Type: ESP Init State: Mature Message ID: 00000766 Parent SN: 6 SPI: FECCD6C8 : 3D713141 <= ESP: 9CB1B757 Algorithm: AES256/SHA512/DH20 TS local: Proto:any, ::-ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff, Ports:any TS remote: Proto:any, ::-ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff, Ports:any Created: Jun.27 09:05:49, 38 minutes 4 seconds ago Expires: Jun.27 10:05:49, rekey in 12 minutes 27 seconds (3031 sec) weberjoh@pa> weberjoh@pa> weberjoh@pa> show vpn ipsec-sa tunnel fg:fg GwID/client IP TnID Peer-Address Tunnel(Gateway) Algorithm SPI(in) SPI(out) life(Sec/KB) -------------- ---- ------------ --------------- --------- ------- -------- ------------ 23 32 2003:51:6012::4 fg:fg(fg) ESP/A256/SHA512 C18C3620 3D713142 3479/0 Show IPSec SA: Total 1 tunnels found. 1 ipsec sa found. weberjoh@pa> weberjoh@pa> weberjoh@pa> show vpn ipsec-sa tunnel fg:fg6 GwID/client IP TnID Peer-Address Tunnel(Gateway) Algorithm SPI(in) SPI(out) life(Sec/KB) -------------- ---- ------------ --------------- --------- ------- -------- ------------ 23 33 2003:51:6012::4 fg:fg6(fg) ESP/A256/SHA512 FECCD6C8 3D713141 891/0 Show IPSec SA: Total 1 tunnels found. 1 ipsec sa found. weberjoh@pa> weberjoh@pa> weberjoh@pa> show vpn tunnel name fg:fg TnID Name Gateway Local Proxy IP Ptl:Port Remote Proxy IP Ptl:Port Proposals ---- ---- ------- -------------- -------- --------------- -------- --------- 32 fg:fg fg 0.0.0.0/0 0:0 0.0.0.0/0 0:0 ESP tunl [DH20][AES256][SHA512] 3600-sec 0-kb Show IPSec tunnel config: Total 1 tunnels found. weberjoh@pa> weberjoh@pa> weberjoh@pa> show vpn tunnel name fg:fg6 TnID Name Gateway Local Proxy IP Ptl:Port Remote Proxy IP Ptl:Port Proposals ---- ---- ------- -------------- -------- --------------- -------- --------- 33 fg:fg6 fg ::/0 0:0 ::/0 0:0 ESP tunl [DH20][AES256][SHA512] 3600-sec 0-kb Show IPSec tunnel config: Total 1 tunnels found. weberjoh@pa> weberjoh@pa> weberjoh@pa> show vpn flow name fg:fg tunnel fg:fg id: 32 type: IPSec gateway id: 23 local ip: 2003:51:6012::2 peer ip: 2003:51:6012::4 inner interface: tunnel.4 outer interface: ethernet1/1 state: active session: 56269 tunnel mtu: 1388 soft lifetime: 3569 hard lifetime: 3600 lifetime remain: 3434 sec lifesize remain: N/A latest rekey: 166 seconds ago monitor: off monitor packets seen: 0 monitor packets reply:0 en/decap context: 40 local spi: C18C3620 remote spi: 3D713142 key type: auto key protocol: ESP auth algorithm: SHA512 enc algorithm: AES256 traffic selector: protocol: 0 local ip range: 0.0.0.0 - 255.255.255.255 local port range: 0 - 65535 remote ip range: 0.0.0.0 - 255.255.255.255 remote port range: 0 - 65535 anti replay check: yes copy tos: no authentication errors: 0 decryption errors: 0 inner packet warnings: 0 replay packets: 0 packets received when lifetime expired:0 when lifesize expired:0 sending sequence: 330 receive sequence: 331 encap packets: 1614770 decap packets: 833356 encap bytes: 1622388048 decap bytes: 806157712 key acquire requests: 1 owner state: 0 owner cpuid: s1dp0 ownership: 1 weberjoh@pa> weberjoh@pa> weberjoh@pa> show vpn flow name fg:fg6 tunnel fg:fg6 id: 33 type: IPSec gateway id: 23 local ip: 2003:51:6012::2 peer ip: 2003:51:6012::4 inner interface: tunnel.4 outer interface: ethernet1/1 state: active session: 31283 tunnel mtu: 1388 soft lifetime: 3522 hard lifetime: 3600 lifetime remain: 842 sec lifesize remain: N/A latest rekey: 2758 seconds ago monitor: off monitor packets seen: 0 monitor packets reply:0 en/decap context: 26 local spi: FECCD6C8 remote spi: 3D713141 key type: auto key protocol: ESP auth algorithm: SHA512 enc algorithm: AES256 traffic selector: protocol: 0 local ip range: :: - ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff local port range: 0 - 65535 remote ip range: :: - ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff remote port range: 0 - 65535 anti replay check: yes copy tos: no authentication errors: 0 decryption errors: 0 inner packet warnings: 0 replay packets: 0 packets received when lifetime expired:0 when lifesize expired:0 sending sequence: 664 receive sequence: 667 encap packets: 735 decap packets: 831360 encap bytes: 99960 decap bytes: 820373328 key acquire requests: 65 owner state: 0 owner cpuid: s1dp0 ownership: 1 weberjoh@pa> |
And this are the outputs from the FortiGate. Note that there seems to be a bug for the get vpn ike gateway command because it resulted in a closed PuTTY session after hundreds of lines! Have a look at the lines 23-37 which I only listed four times here:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 |
fg # get vpn ike gateway pa vd: root/0 name: pa version: 2 interface: wan1 6 addr: 2003:51:6012::4:500 -> 2003:51:6012::2:500 created: 60946s ago IKE SA created: 1/3 established: 1/3 time: 0/226/680 ms IPsec SA created: 2/38 established: 2/38 time: 0/68/1240 ms id/spi: 95 257d196a85066784/4175cd992c3c06f4 direction: responder status: established 12286-12286s ago = 0ms proposal: aes-256-sha512 SK_ei: fba5cabf2b055cfb-6f2f685296f4b93e-47527a8d4ada2970-e93c91cf6a6d8aef SK_er: 6a938f311ccaab3d-93cf2341d2237452-d4bd557112c3f3d7-8959a4f85c8c7d8d SK_ai: 9b6b147b61ba9237-248c4823ce761143-5fd2ac9117fc5a6d-c8e94ac7729c84e5-6b651712de89ae51-71a4af5f21ee2973-872e30df0f417c87-ed285218e88812b8 SK_ar: 3bbdf19282cdb031-3b04c65772e18b84-7aebb082fea024b0-fb5f29ab0e873ccf-67f648fdbe8b602b-fec8468e33bfa48d-9d36f1931253951e-7d0a252edce42933 lifetime/rekey: 28800/16243 DPD sent/recv: 000000f5/000000f5 id/spi: 0 0000000000000000/0000000000000000 direction: responder status: connecting, state 0, started 0s ago id/spi: 0 0000000000000000/0000000000000000 direction: responder status: connecting, state 0, started 0s ago id/spi: 0 0000000000000000/0000000000000000 direction: responder status: connecting, state 0, started 0s ago id/spi: 0 0000000000000000/0000000000000000 direction: responder status: connecting, state 0, started 0s ago [...] fg # fg # fg # get vpn ipsec tunnel name pa gateway name: 'pa' type: route-based local-gateway: 2003:51:6012::4:0 (static) remote-gateway: 2003:51:6012::2:0 (static) mode: ike-v2 interface: 'wan1' (6) rx packets: 16084 bytes: 3003520 errors: 0 tx packets: 16151 bytes: 1830681 errors: 0 dpd: on-demand/negotiated idle: 20000ms retry: 3 count: 0 selectors name: 'pa' auto-negotiate: enable mode: tunnel src: 0:0.0.0.0/0.0.0.0:0 dst: 0:0.0.0.0/0.0.0.0:0 SA lifetime/rekey: 3600/1665 mtu: 1390 tx-esp-seq: eed replay: enabled inbound spi: 3d713144 enc: aes-cb 4a823372f691c3006db1e32c3c5bb4dc957dfa61e8f1484b75f0883eb7536cc6 auth: sha512 e8f03430854a9411765cd4689da2c64f78070e9e45e2c1e973bf83cb6b969464aadccd00ee2b846d55c8c695251ad00657f539611254eb8e76da8ac61abe078d outbound spi: fd69edff enc: aes-cb acab60bfcfddb9f485f296528b84bf31f4a5f2e5a13173d1d2dc824358785e9c auth: sha512 158ab9b65c11d92d67c9199768a13bab72251311f4b4bbec8dc9002ed64391bf85365a5abe4baf5ec55f09c46571058412690fbdae28eafaebf471abe2592b17 NPU acceleration: none selectors name: 'pa6' auto-negotiate: enable mode: tunnel src: 0:::/0:0 dst: 0:::/0:0 SA lifetime/rekey: 3600/2206 mtu: 1390 tx-esp-seq: 557 replay: enabled inbound spi: 3d713145 enc: aes-cb 30a8116f7312aa705fb3ea94fe9d0212347912f657499dd2290dd50e94f4a801 auth: sha512 07335a32925f88eeac7e753273457f4a49f01a71db5397b7606cc7e0c30ef51525db0ae6f887d4862e292869014741fcfce4adb00b42cac5daa04a2a67ececc3 outbound spi: d48144de enc: aes-cb cf9a0c704dcddad8f28e6e40034c53afe8e28c6bb10626c35dcaf62dbf1d37dd auth: sha512 e0b2ebe3d044d5832e6e26512909a48a1537a819f636b31fbdb42adbf44c21a949516ff1daf0501536d0441d0ddf83aca2b8bbe810a6d5c48004ad379acef264 NPU acceleration: none fg # |
Featured image: “In die Röhre gucken” by Silke is licensed under CC BY-ND 2.0.



Hi,
Vey very nice blog!!
Hi there,I enjoy reading through your article post, I wanted to write a little comment to support you and wish you a good continuationAll the best for all your blogging efforts.
Appreciate the recommendation! Let me try it out.
Keep working ,great job!
Fortinet network security providers India