I am using the WHOIS client a lot these days since I am migrating some RIPE objects such as ASes, inetnum/inet6num, etc. Meanwhile, I recognized that I have never captured this TCP port 43 protocol, nor looked at it with Wireshark. That’s what this post is all about, incl. a downloadable pcap for your own analysis.
For this trace, I basically queried a couple of different names which resulted in a couple of different WHOIS queries to *some* destinations. To be honest, I don’t know exactly which destinations are chosen, but this seems to be correct. ;) Citing the manpage of whois: “the whois client tries to guess the right server to ask for the specified object”. If you are interested in more details of the tool itself, please have a look at:
- RFC 3912: WHOIS Protocol Specification
- RIPE Database Query Reference Manual
- Computer Hope: Linux whois command
- Wikipedia: WHOIS
Basically, WHOIS is a telnet-like TCP protocol running at port 43. Single query – single response. It is not encrypted at all but in plain text. Since all queried information is public anyway, that’s not a big deal. (However, a passive attacker can record which queries you’re sending.)
Download the pcap, 7zipped, 21 KB. I left all those surrounding DNS and ICMP packets in there intentionally:
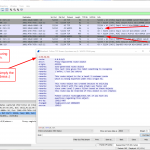
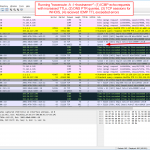
Wireshark screenshots:
Demo Requests
These are the queries you’ll find in the trace. Besides querying the keywords that the server supports, I asked for some domains of different TLDs (which failed for *.blog), IPv4 and IPv6 networks, an ASN, a RIPE handle (which worked with the -a option) and a full name (which is quite common in German and hence lists many different persons):
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 |
whois -q version whois -q types whois -q sources whois weberlab.de whois weberblog.net whois netsec.blog whois apnic.net whois 193.24.227.230 whois 2003:51:6012::/48 whois 2001:dd8:9:2::101:61 whois AS31054 whois JW2311 whois -a JW2311 whois -a Klaus Mueller |
Here is the full listing with all answeres: (Grr, for whatever reason after each line starting with a %, the listing plugin adds a newline. Sorry.)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 332 333 334 335 336 337 338 339 340 341 342 343 344 345 346 347 348 349 350 351 352 353 354 355 356 357 358 359 360 361 362 363 364 365 366 367 368 369 370 371 372 373 374 375 376 377 378 379 380 381 382 383 384 385 386 387 388 389 390 391 392 393 394 395 396 397 398 399 400 401 402 403 404 405 406 407 408 409 410 411 412 413 414 415 416 417 418 419 420 421 422 423 424 425 426 427 428 429 430 431 432 433 434 435 436 437 438 439 440 441 442 443 444 445 446 447 448 449 450 451 452 453 454 455 456 457 458 459 460 461 462 463 464 465 466 467 468 469 470 471 472 473 474 475 476 477 478 479 480 481 482 483 484 485 486 487 488 489 490 491 492 493 494 495 496 497 498 499 500 501 502 503 504 505 506 507 508 509 510 511 512 513 514 515 516 517 518 519 520 521 522 523 524 525 526 527 528 529 530 531 532 533 534 535 536 537 538 539 540 541 542 543 544 545 546 547 548 549 550 551 552 553 554 555 556 557 558 559 560 561 562 563 564 565 566 567 568 569 570 571 572 573 574 575 576 577 578 579 580 581 582 583 584 585 586 587 588 589 590 591 592 593 594 595 596 597 598 599 600 601 602 603 604 605 606 607 608 609 610 611 612 613 614 615 616 617 618 619 620 621 622 623 624 625 626 627 628 629 630 631 632 633 634 635 636 637 638 639 640 641 642 643 644 645 646 647 648 649 650 651 652 653 654 655 656 657 658 659 660 661 662 663 664 665 666 667 668 669 670 671 672 673 674 675 676 677 678 679 680 681 682 683 684 685 686 687 688 689 690 691 692 693 694 695 696 697 698 699 700 701 702 703 704 705 706 707 708 709 710 711 712 713 714 715 716 717 718 719 720 721 722 723 724 725 726 727 728 729 730 731 732 733 734 735 736 737 738 739 740 741 742 743 744 745 746 747 748 749 750 751 752 753 754 755 756 757 758 759 760 761 762 763 764 765 766 767 768 769 770 771 772 773 774 775 776 777 778 779 780 781 782 783 784 785 786 787 788 789 790 791 792 793 794 795 796 797 798 799 800 801 802 803 804 805 806 807 808 809 810 811 812 813 814 815 816 817 818 819 820 821 822 823 824 825 826 827 828 829 830 831 832 833 834 835 836 837 838 839 840 841 842 843 844 845 846 847 848 849 850 851 852 853 854 855 856 857 858 859 860 861 862 863 864 865 866 867 868 |
weberjoh@nb15-lx:~$ whois -q version % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf % whois-server-1.96 % This query was served by the RIPE Database Query Service version 1.96 (WAGYU) weberjoh@nb15-lx:~$ whois -q types % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf inetnum inet6num as-block aut-num as-set route route6 route-set inet-rtr filter-set peering-set rtr-set domain poetic-form poem mntner irt key-cert organisation role person % This query was served by the RIPE Database Query Service version 1.96 (BLAARKOP) weberjoh@nb15-lx:~$ whois -q sources % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf RIPE:3:N:0-0 RIPE-NONAUTH:3:N:0-0 AFRINIC-GRS:3:N:0-0 APNIC-GRS:3:N:0-0 ARIN-GRS:3:N:0-0 JPIRR-GRS:3:N:0-0 LACNIC-GRS:3:N:0-0 RADB-GRS:3:N:0-0 RIPE-GRS:3:N:0-0 % This query was served by the RIPE Database Query Service version 1.96 (ANGUS) weberjoh@nb15-lx:~$ whois weberlab.de % Restricted rights. % % Terms and Conditions of Use % % The above data may only be used within the scope of technical or % administrative necessities of Internet operation or to remedy legal % problems. % The use for other purposes, in particular for advertising, is not permitted. % % The DENIC whois service on port 43 doesn't disclose any information concerning % the domain holder, general request and abuse contact. % This information can be obtained through use of our web-based whois service % available at the DENIC website: % http://www.denic.de/en/domains/whois-service/web-whois.html % % Domain: weberlab.de Nserver: ns1.weberdns.de Nserver: ns2.weberdns.de Dnskey: 257 3 10 AwEAAd3v/e0irXYKOwtYEB3VPe7z99qvi5le9/y1XXyplp5y/5xaqrm/relG8pgx8GsNW2IgviJKAJ6UiU45ERKoH+fz2qf2SUFHFWwkweiWyLZ4EZHhowviCEx94P4OswNKXmdYHe38rlHPa+3OypW9gYfR9lhCKK3neCPq8/aFFsTTI7dQ+Q2kERWiCMCybl4WOwsBo/RlnPM4yufMKIlABiM5NWQPNmI6jYzAYpYoyUhd9HnnIIDlNQ89HpXQdFmysMraXYb7qDOoOEiOodttKH0y/vtJ2SRU05RF4AEumacIUzAi5LL2cMQxC7t7rlDI4X42NRfOLAqGuOeclFjzqz3OdAJWeg/AAnSbb02AGCkQ370TX1hWveAXt6xpPWOLgHXSLIF/lz+wl+Dm8ZNWDnn5zEJuEj3xova1g8zmRXJOmqA6VhGqewxF8c+yKeNEOHz4X4/RLmWHIuEbvboP00Dk5A9bhyZGVsytOJg+NwhFQtvBWLmD82FFtfSt2vmbFFNwAZOnRZWJOG9L7TFcGIm1OEULmohUyFLsBGMXDFOu1k0o6pqm495tsBuMyJNpfdQoPwOkUpsKi6jmNq6vRjvvNiJbcFylTQrqHGTGuOopuUsBbUXj/nOr4I6j42k6GDIuTyLDkaVrdrxXmGnfNnStdqWmvHXo/YFwdls9bcT7 Status: connect Changed: 2018-12-06T13:58:44+01:00 weberjoh@nb15-lx:~$ whois weberblog.net Domain Name: WEBERBLOG.NET Registry Domain ID: 2309456774_DOMAIN_NET-VRSN Registrar WHOIS Server: whois.meshdigital.com Registrar URL: http://www.meshdigital.com Updated Date: 2018-11-18T05:52:18Z Creation Date: 2018-09-12T21:46:59Z Registry Expiry Date: 2020-09-12T21:46:59Z Registrar: Mesh Digital Limited Registrar IANA ID: 1390 Registrar Abuse Contact Email: Registrar Abuse Contact Phone: Domain Status: ok https://icann.org/epp#ok Name Server: NS1.HANS.HOSTEUROPE.DE Name Server: NS2.HANS.HOSTEUROPE.DE DNSSEC: unsigned URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/ >>> Last update of whois database: 2019-12-20T14:58:20Z <<< For more information on Whois status codes, please visit https://icann.org/epp NOTICE: The expiration date displayed in this record is the date the registrar's sponsorship of the domain name registration in the registry is currently set to expire. This date does not necessarily reflect the expiration date of the domain name registrant's agreement with the sponsoring registrar. Users may consult the sponsoring registrar's Whois database to view the registrar's reported date of expiration for this registration. TERMS OF USE: You are not authorized to access or query our Whois database through the use of electronic processes that are high-volume and automated except as reasonably necessary to register domain names or modify existing registrations; the Data in VeriSign Global Registry Services' ("VeriSign") Whois database is provided by VeriSign for information purposes only, and to assist persons in obtaining information about or related to a domain name registration record. VeriSign does not guarantee its accuracy. By submitting a Whois query, you agree to abide by the following terms of use: You agree that you may use this Data only for lawful purposes and that under no circumstances will you use this Data to: (1) allow, enable, or otherwise support the transmission of mass unsolicited, commercial advertising or solicitations via e-mail, telephone, or facsimile; or (2) enable high volume, automated, electronic processes that apply to VeriSign (or its computer systems). The compilation, repackaging, dissemination or other use of this Data is expressly prohibited without the prior written consent of VeriSign. You agree not to use electronic processes that are automated and high-volume to access or query the Whois database except as reasonably necessary to register domain names or modify existing registrations. VeriSign reserves the right to restrict your access to the Whois database in its sole discretion to ensure operational stability. VeriSign may restrict or terminate your access to the Whois database for failure to abide by these terms of use. VeriSign reserves the right to modify these terms at any time. The Registry database contains ONLY .COM, .NET, .EDU domains and Registrars. weberjoh@nb15-lx:~$ whois netsec.blog No whois server is known for this kind of object. weberjoh@nb15-lx:~$ whois apnic.net Domain Name: APNIC.NET Registry Domain ID: 2142030_DOMAIN_NET-VRSN Registrar WHOIS Server: whois.name.com Registrar URL: http://www.name.com Updated Date: 2019-07-28T22:12:21Z Creation Date: 1993-08-27T04:00:00Z Registry Expiry Date: 2021-08-26T04:00:00Z Registrar: Name.com, Inc. Registrar IANA ID: 625 Registrar Abuse Contact Email: abuse@name.com Registrar Abuse Contact Phone: 7202492374 Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited Name Server: APNIC.AUTHDNS.RIPE.NET Name Server: NETNOD.APNIC.NET Name Server: NS2.APNIC.NET Name Server: NS4.APNIC.NET DNSSEC: signedDelegation DNSSEC DS Data: 53839 13 2 CA144D6C226FED85E326B8E214F6B20C7F265EAFE198CC501B6756C3C8578108 URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/ >>> Last update of whois database: 2019-12-20T14:58:20Z <<< For more information on Whois status codes, please visit https://icann.org/epp NOTICE: The expiration date displayed in this record is the date the registrar's sponsorship of the domain name registration in the registry is currently set to expire. This date does not necessarily reflect the expiration date of the domain name registrant's agreement with the sponsoring registrar. Users may consult the sponsoring registrar's Whois database to view the registrar's reported date of expiration for this registration. TERMS OF USE: You are not authorized to access or query our Whois database through the use of electronic processes that are high-volume and automated except as reasonably necessary to register domain names or modify existing registrations; the Data in VeriSign Global Registry Services' ("VeriSign") Whois database is provided by VeriSign for information purposes only, and to assist persons in obtaining information about or related to a domain name registration record. VeriSign does not guarantee its accuracy. By submitting a Whois query, you agree to abide by the following terms of use: You agree that you may use this Data only for lawful purposes and that under no circumstances will you use this Data to: (1) allow, enable, or otherwise support the transmission of mass unsolicited, commercial advertising or solicitations via e-mail, telephone, or facsimile; or (2) enable high volume, automated, electronic processes that apply to VeriSign (or its computer systems). The compilation, repackaging, dissemination or other use of this Data is expressly prohibited without the prior written consent of VeriSign. You agree not to use electronic processes that are automated and high-volume to access or query the Whois database except as reasonably necessary to register domain names or modify existing registrations. VeriSign reserves the right to restrict your access to the Whois database in its sole discretion to ensure operational stability. VeriSign may restrict or terminate your access to the Whois database for failure to abide by these terms of use. VeriSign reserves the right to modify these terms at any time. The Registry database contains ONLY .COM, .NET, .EDU domains and Registrars. weberjoh@nb15-lx:~$ whois 193.24.227.230 % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf % Note: this output has been filtered. % To receive output for a database update, use the "-B" flag. % Information related to '193.24.224.0 - 193.24.227.255' % Abuse contact for '193.24.224.0 - 193.24.227.255' is 'abuse@arcor-ip.de' inetnum: 193.24.224.0 - 193.24.227.255 netname: HELPAG country: DE org: ORG-TRiG1-RIPE admin-c: TLA126-RIPE tech-c: TLA126-RIPE status: ASSIGNED PI mnt-by: RIPE-NCC-END-MNT mnt-by: HELPAG-MNT mnt-by: DE-COLT-MNT mnt-routes: HELPAG-MNT mnt-domains: HELPAG-MNT created: 2004-02-16T10:08:31Z last-modified: 2016-04-14T11:14:20Z source: RIPE sponsoring-org: ORG-MAT1-RIPE organisation: ORG-TRiG1-RIPE org-name: TUEV Rheinland i-sec GmbH org-type: OTHER address: Zum Wartturm 9 address: 63571 Gelnhausen address: Germany abuse-c: AR26941-RIPE mnt-ref: ARCOR-MNT mnt-by: ARCOR-MNT created: 2012-04-18T06:13:55Z last-modified: 2014-11-17T22:28:06Z source: RIPE # Filtered person: Thomas Laubrock address: Zum Warttrum 9, 63571 Gelnhausen mnt-by: HELPAG-MNT phone: +49 6051 974929 nic-hdl: TLA126-RIPE created: 2010-12-02T16:57:47Z last-modified: 2011-02-23T14:25:35Z source: RIPE # Filtered % Information related to '193.24.224.0/22AS31054' route: 193.24.224.0/22 descr: HELPAG-NET origin: AS31054 mnt-by: HELPAG-MNT created: 2004-06-25T11:34:39Z last-modified: 2004-06-25T11:34:39Z source: RIPE % This query was served by the RIPE Database Query Service version 1.96 (ANGUS) weberjoh@nb15-lx:~$ whois 2003:51:6012::/48 % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf % Note: this output has been filtered. % To receive output for a database update, use the "-B" flag. % Information related to '2003:51:6012::/48' % Abuse contact for '2003:51:6012::/48' is 'auftrag@nic.telekom.de' inet6num: 2003:51:6012::/48 netname: BUNDESBANK-NERZ-FRANKFURT-NET descr: TSI fuer Deutsche Bundesbank country: DE admin-c: IS4265-RIPE tech-c: IS4265-RIPE status: ASSIGNED mnt-by: DTAG-NIC created: 2018-03-06T09:10:55Z last-modified: 2018-03-06T09:10:55Z source: RIPE # Filtered person: Ingolf Stange address: e-Shelter co. Dt.Bundesbank address: Eschborner Landstr. 100 address: 60489 Frankfurt address: DE phone: +498928892394 fax-no: +49697090972394 nic-hdl: IS4265-RIPE mnt-by: DTAG-NIC created: 2013-01-28T10:28:05Z last-modified: 2013-01-28T10:28:05Z source: RIPE # Filtered % Information related to '2003::/23AS3320' route6: 2003::/23 descr: DTAG European region optimized origin: AS3320 member-of: AS3320:RS-PA-TELEKOM-REGIONALS mnt-by: DTAG-RR created: 2014-02-20T18:06:20Z last-modified: 2014-02-20T18:06:20Z source: RIPE % This query was served by the RIPE Database Query Service version 1.96 (BLAARKOP) weberjoh@nb15-lx:~$ whois 2001:dd8:9:2::101:61 % [whois.apnic.net] % Whois data copyright terms http://www.apnic.net/db/dbcopyright.html % Information related to '2001:dd8:8::/45' % Abuse contact for '2001:dd8:8::/45' is 'noc@apnic.net' inet6num: 2001:dd8:8::/45 netname: APNIC-SERVICES-AU descr: Asia Pacific Network Information Centre descr: Regional Internet Registry for the Asia-Pacific Region descr: 6 Cordelia Street descr: PO Box 3646 descr: South Brisbane, QLD 4101 descr: Australia country: AU org: ORG-APNI1-AP admin-c: AIC1-AP tech-c: AIC1-AP mnt-by: APNIC-HM mnt-routes: MAINT-APNIC-IS-AP mnt-irt: IRT-APNIC-IS-AP status: ASSIGNED PORTABLE last-modified: 2018-10-08T03:16:31Z source: APNIC irt: IRT-APNIC-IS-AP remarks: APNIC Infrastructure Services address: South Brisbane, Australia e-mail: noc@apnic.net abuse-mailbox: noc@apnic.net admin-c: AIC1-AP tech-c: AIC1-AP auth: # Filtered mnt-by: MAINT-APNIC-IS-AP last-modified: 2018-11-04T23:43:29Z source: APNIC organisation: ORG-APNI1-AP org-name: Asia Pacific Network Information Centre remarks: APNIC Infrastructure Services country: AU address: 6 Cordelia Street phone: +61-7-3858-3100 fax-no: +61-7-3858-3199 e-mail: noc@apnic.net mnt-ref: APNIC-HM mnt-by: APNIC-HM last-modified: 2018-06-06T05:06:58Z source: APNIC role: APNIC Infrastructure Contact address: 6 Cordelia Street address: South Brisbane address: QLD 4101 country: AU phone: +61 7 3858 3100 fax-no: +61 7 3858 3199 e-mail: noc@apnic.net admin-c: HM20-AP tech-c: NO4-AP nic-hdl: AIC1-AP mnt-by: MAINT-APNIC-IS-AP last-modified: 2018-10-08T02:52:19Z source: APNIC % Information related to '2001:dd8:9::/48AS4608' route6: 2001:dd8:9::/48 descr: APNIC Network country: AU origin: AS4608 mnt-by: MAINT-APNIC-IS-AP last-modified: 2018-11-20T03:36:54Z source: APNIC % This query was served by the APNIC Whois Service version 1.88.15-46 (WHOIS-UK4) weberjoh@nb15-lx:~$ whois AS31054 % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf % Note: this output has been filtered. % To receive output for a database update, use the "-B" flag. % Information related to 'AS31000 - AS31064' as-block: AS31000 - AS31064 descr: RIPE NCC ASN block remarks: These AS Numbers are assigned to network operators in the RIPE NCC service region. mnt-by: RIPE-NCC-HM-MNT created: 2018-11-22T15:27:33Z last-modified: 2018-11-22T15:27:33Z source: RIPE % Information related to 'AS31054' % Abuse contact for 'AS31054' is 'abuse@arcor-ip.de' aut-num: AS31054 as-name: HELPAG-AS org: ORG-TRIG1-RIPE import: from AS3209 action pref=100; accept any export: to AS3209 announce AS31054 import: from AS8196 action pref=100; accept any export: to AS8196 announce AS31054 admin-c: TLA126-RIPE tech-c: TLA126-RIPE status: ASSIGNED mnt-by: RIPE-NCC-END-MNT mnt-by: HELPAG-MNT mnt-by: DE-COLT-MNT created: 2004-02-16T12:50:14Z last-modified: 2018-09-04T10:00:53Z source: RIPE sponsoring-org: ORG-MAT1-RIPE organisation: ORG-TRiG1-RIPE org-name: TUEV Rheinland i-sec GmbH org-type: OTHER address: Zum Wartturm 9 address: 63571 Gelnhausen address: Germany abuse-c: AR26941-RIPE mnt-ref: ARCOR-MNT mnt-by: ARCOR-MNT created: 2012-04-18T06:13:55Z last-modified: 2014-11-17T22:28:06Z source: RIPE # Filtered person: Thomas Laubrock address: Zum Warttrum 9, 63571 Gelnhausen mnt-by: HELPAG-MNT phone: +49 6051 974929 nic-hdl: TLA126-RIPE created: 2010-12-02T16:57:47Z last-modified: 2011-02-23T14:25:35Z source: RIPE # Filtered % This query was served by the RIPE Database Query Service version 1.96 (WAGYU) weberjoh@nb15-lx:~$ whois JW2311 No whois server is known for this kind of object. weberjoh@nb15-lx:~$ whois -a JW2311 % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf % Note: this output has been filtered. % To receive output for a database update, use the "-B" flag. % Information related to 'JW2311' person: Johannes Weber address: Freigerichter Str. 1-3 address: 63571 address: Gelnhausen address: GERMANY phone: +49 174 1880211 nic-hdl: JW2311 mnt-by: mnt-de-tr-isec-1 created: 2019-09-17T12:43:49Z last-modified: 2019-09-17T12:56:01Z source: RIPE # Filtered % This query was served by the RIPE Database Query Service version 1.96 (WAGYU) weberjoh@nb15-lx:~$ whois -a Klaus Mueller % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf % Note: this output has been filtered. % To receive output for a database update, use the "-B" flag. % Information related to 'KM1011-RIPE' person: Klaus Mueller address: Metrax GmbH - Medical Systems address: Rheinwaldstrasse 22 address: DE 78628 Rottweil address: Germany phone: +49 7171 402 296 fax-no: +49 7171 9402 296 nic-hdl: KM1011-RIPE created: 1970-01-01T00:00:00Z last-modified: 2016-04-05T16:11:42Z mnt-by: RIPE-NCC-LOCKED-MNT source: RIPE % Information related to 'KM125-RIPE' person: Klaus Mueller address: Lernstudio Barbarossa / MegaKids Computerschule GmbH address: Luxemburger Stra▒e 1-3 address: 67657 Kaiserslautern address: GERMANY phone: +49-631-362410 nic-hdl: KM125-RIPE mnt-by: inexio-mnt created: 2009-07-23T08:20:32Z last-modified: 2010-10-04T14:09:43Z source: RIPE # Filtered % Information related to 'KM1538-RIPE' person: Klaus Mueller address: Wasserwerk Gerauer Land address: Breslauer Str.10 address: 64521 Gro▒-Gerau address: Germany phone: +49 6152981726 fax-no: +49 6152981734 nic-hdl: KM1538-RIPE mnt-by: TITANNET-MNT created: 2004-08-16T09:34:16Z last-modified: 2009-05-14T11:58:02Z source: RIPE # Filtered % Information related to 'KM1563-RIPE' person: KLAUS MUELLER address: DIMA SERVICE AG address: HAGENTHALERSTR 150 address: 4124 SCH▒NENBUCH address: Switzerland phone: +41 0617662525 nic-hdl: KM1563-RIPE created: 2004-09-06T16:05:50Z last-modified: 2016-04-06T15:30:03Z mnt-by: RIPE-NCC-LOCKED-MNT source: RIPE % Information related to 'KM1567-RIPE' person: KLAUS MUELLER address: DIMA SERVICE AG address: HAGENTHALERSTR 150 address: 4124 SCHOENENBUCH address: Switzerland phone: +41 0617612577 nic-hdl: KM1567-RIPE created: 2004-09-08T09:05:33Z last-modified: 2016-04-06T15:32:13Z mnt-by: RIPE-NCC-LOCKED-MNT source: RIPE % Information related to 'KM1571-RIPE' person: KLAUS MUELLER address: DIMA SERVICE AG address: HAGENTHALERSTRASSE 150 address: 4124 SCHOENENBUCH address: Switzerland phone: +41 0617860013 nic-hdl: KM1571-RIPE created: 2004-09-08T22:10:30Z last-modified: 2016-04-06T15:32:46Z mnt-by: RIPE-NCC-LOCKED-MNT source: RIPE % Information related to 'KM2307-RIPE' person: Klaus Mueller address: Schwarz + Hansen GmbH address: Billstrasse 148 address: D-20539 Hamburg address: GERMANY phone: +49 40 7812114 nic-hdl: KM2307-RIPE mnt-by: HANSENET-NOC created: 2006-11-16T13:22:22Z last-modified: 2012-01-02T06:26:20Z source: RIPE # Filtered % Information related to 'KM2332-RIPE' person: Klaus Mueller address: Le Patron Regina AG address: Rohrmattstrasse 1 address: CH-4461 Boeckten address: Switzerland phone: +41 61 985 85 85 fax-no: +41 61 985 85 86 nic-hdl: KM2332-RIPE mnt-by: CH-GREEN-MNT created: 1970-01-01T00:00:00Z last-modified: 2012-09-29T02:40:03Z source: RIPE % Information related to 'KM2360-RIPE' person: Klaus Mueller address: Phonework GmbH address: Sebastian-Tiefenthaler-Str. 11 address: D-83101 Rohrdorf address: Germany phone: +49.8031901800 fax-no: +49.803190180180 nic-hdl: KM2360-RIPE mnt-by: MNET-MNT created: 2007-07-04T14:50:25Z last-modified: 2007-07-04T14:50:25Z source: RIPE # Filtered % Information related to 'KM2638-RIPE' person: Klaus Mueller address: TWT Digital Health GmbH address: Im Schuhmachergewann 6 address: 69123 Heidelberg address: GERMANY phone: +49 6221 822020 fax-no: +49 6221 822040 nic-hdl: KM2638-RIPE mnt-by: MNT-PlusServer created: 2007-12-09T19:39:55Z last-modified: 2019-01-24T08:05:21Z source: RIPE # Filtered % Information related to 'KM275-RIPE' person: Klaus Mueller address: Roemer Etikett GmbH Elnhausen address: DE 35041 Marburg phone: +49 6420 8232 27 fax-no: +49 6420 8232 82 nic-hdl: KM275-RIPE created: 1970-01-01T00:00:00Z last-modified: 2016-04-05T14:54:14Z mnt-by: RIPE-NCC-LOCKED-MNT source: RIPE % Information related to 'KM3976-RIPE' person: Klaus Mueller address: Pure Nature Products Versand GmbH address: Zur Rothheck 14 address: 55743 Idar-Oberstein address: DE phone: +49 6781 983990 nic-hdl: KM3976-RIPE mnt-by: DTAG-NIC created: 2012-02-28T13:58:18Z last-modified: 2012-02-28T13:58:18Z source: RIPE # Filtered % Information related to 'KM5813-RIPE' person: Klaus Mueller address: EBRA-Dienstleistungen GmbH & Co.KG address: Freiburger Str. 28 /1 address: 88400 Biberach an der Riss address: DE phone: +49 751359530 nic-hdl: KM5813-RIPE mnt-by: DTAG-NIC created: 2015-04-14T05:55:51Z last-modified: 2015-04-14T05:55:51Z source: RIPE # Filtered % Information related to 'KM6262-RIPE' person: Klaus Mueller address: P.W. Hieronimi Moderner Baubedarf GmbH address: Industriestr. 7 address: 54486 Muelheim address: DE phone: +49 2671 60640 nic-hdl: KM6262-RIPE mnt-by: DTAG-NIC created: 2015-12-28T08:28:25Z last-modified: 2015-12-28T08:28:25Z source: RIPE # Filtered % Information related to 'KM6777-RIPE' person: Klaus Mueller address: IST METZ GmbH address: Lauterstr. 18 address: 72622 Nuertingen address: IST METZ GmbH address: 72622 Nuertingen phone: +4970226002450 fax-no: +497022600276 nic-hdl: KM6777-RIPE mnt-by: DTAG-NIC created: 2016-10-18T11:25:40Z last-modified: 2016-10-18T11:25:40Z source: RIPE # Filtered % Information related to 'KM8474-RIPE' person: Klaus Mueller address: Kastanienallee, 16567, Muehlenbecker Land, Deutschland phone: +49 33056 86211 mnt-by: DTAG-NIC nic-hdl: KM8474-RIPE created: 2019-02-07T12:26:29Z last-modified: 2019-02-07T12:26:29Z source: RIPE # Filtered % Information related to 'KM969-RIPE' person: Klaus Mueller address: IDG Informationsverarbeitung address: Gothaer Allee 1 address: 50969 Koln address: DE phone: +49 221 3082171 nic-hdl: KM969-RIPE mnt-by: EU-IBM-NIC-MNT2 created: 1970-01-01T00:00:00Z last-modified: 2001-09-21T23:40:17Z source: RIPE % Information related to 'MK19800-RIPE' person: Mueller Klaus address: Brigitte Exclusiv AG address: Gossau address: Switzerland phone: +004972313031712 nic-hdl: MK19800-RIPE created: 2016-11-02T10:40:52Z last-modified: 2016-11-02T10:40:52Z source: RIPE # Filtered mnt-by: AS6730-MNT % This query was served by the RIPE Database Query Service version 1.96 (WAGYU) |
Real World Use Case: traceroute -A
One major, but probably unknown, use case of WHOIS is the traceroute tool when performed with the -A option to perform AS path lookups in routing registries. It then does not only issue IP packets with increased hop limits (and printing the ICMP hop limit exceeded error messages) but also sends WHOIS queries along with DNS PTR requests.
Two demo runs in the trace:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 |
weberjoh@nb15-lx:~$ sudo traceroute -A -I cisco.com traceroute to cisco.com (72.163.4.185), 30 hops max, 60 byte packets 1 193.24.227.225 (193.24.227.225) [AS31054] 1.903 ms 1.912 ms 1.912 ms 2 gw.bb01.helpag.de (193.24.227.1) [AS31054] 2.281 ms 2.373 ms 2.278 ms 3 host-212-114-159-13.customer.m-online.net (212.114.159.13) [AS8767] 2.494 ms 2.496 ms 2.484 ms 4 ae1.r3.muc7.m-online.net (82.135.16.242) [AS8767] 9.252 ms 9.270 ms 9.250 ms 5 ae52.bar1.munich1.level3.net (62.140.24.49) [AS3356/AS9057] 9.368 ms 9.367 ms 9.366 ms 6 ae-3-5.edge5.dallas3.level3.net (4.69.208.229) [AS3356] 125.473 ms 123.649 ms 123.552 ms 7 cisco-syste.edge5.dallas3.level3.net (4.59.34.66) [AS3356] 124.047 ms 124.019 ms 123.997 ms 8 rcdn9-cd1-cbb-gw1-ten0-0-0-12.cisco.com (72.163.0.5) [AS109/AS198949] 124.814 ms 124.987 ms 124.964 ms 9 72.163.0.98 (72.163.0.98) [AS109/AS198949] 124.931 ms 124.951 ms 124.927 ms 10 rcdn9-cd1-dmzdcc-gw1-por1.cisco.com (72.163.0.178) [AS109/AS198949] 124.862 ms 124.971 ms 124.849 ms 11 rcdn9-16b-dcz05n-gw2-por1.cisco.com (72.163.2.102) [AS109/AS198949] 124.436 ms 124.527 ms 124.415 ms 12 redirect-ns.cisco.com (72.163.4.185) [AS109] 125.459 ms 124.890 ms 124.842 ms weberjoh@nb15-lx:~$ weberjoh@nb15-lx:~$ weberjoh@nb15-lx:~$ sudo traceroute -6 -A -I cisco.com traceroute to cisco.com (2001:420:1101:1::185), 30 hops max, 80 byte packets 1 pa-dmz.weberlab.de (2001:470:765b::1) [AS6939] 1.560 ms 1.550 ms 1.545 ms 2 router1-trust.weberlab.de (2001:470:1f0b:1024::1) [AS6939] 2.508 ms 2.822 ms 3.028 ms 3 tunnel512279.tunnel.tserv6.fra1.ipv6.he.net (2001:470:1f0a:101a::1) [AS6939] 8.867 ms 13.649 ms 18.468 ms 4 10ge3-18.core1.fra1.he.net (2001:470:0:69::1) [AS6939] 13.795 ms 18.485 ms 18.468 ms 5 100ge11-1.core1.fra2.he.net (2001:470:0:404::2) [AS6939] 18.577 ms 18.597 ms 19.070 ms 6 e0-53.core1.ams2.he.net (2001:470:0:4b7::2) [AS6939] 25.088 ms * * 7 100ge8-1.core1.lon3.he.net (2001:470:0:227::1) [AS6939] 12.850 ms 13.012 ms 12.888 ms 8 100ge14-1.core1.lon2.he.net (2001:470:0:3ea::1) [AS6939] 12.903 ms 28.117 ms 27.983 ms 9 100ge13-2.core1.nyc4.he.net (2001:470:0:2cf::2) [AS6939] 102.899 ms 101.014 ms 100.989 ms 10 * * as7018-att.10gigabitethernet2-3.core1.nyc4.he.net (2001:470:0:1dd::2) [AS6939] 85.198 ms 11 n54ny22crs.ipv6.att.net (2001:1890:ff:ffff:12:122:130:170) [AS7018] 124.521 ms 125.916 ms 125.850 ms 12 wswdc22crs.ipv6.att.net (2001:1890:ff:ffff:12:122:28:42) [AS7018] 123.780 ms 123.794 ms 123.782 ms 13 attga21crs.ipv6.att.net (2001:1890:ff:ffff:12:122:2:29) [AS7018] 125.699 ms 125.714 ms 125.692 ms 14 dlstx22crs.ipv6.att.net (2001:1890:ff:ffff:12:122:2:110) [AS7018] 122.889 ms 122.921 ms 122.914 ms 15 dlstx408me9.ipv6.att.net (2001:1890:ff:ffff:12:122:118:121) [AS7018] 120.233 ms 119.705 ms 119.088 ms 16 * * * 17 rcdn9-cd2-cbb-gw2-ten-0-0-0-26.cisco.com (2001:420:1100:a::1) [AS109] 120.497 ms 120.522 ms 120.690 ms 18 2001:420:1100:1e::1 (2001:420:1100:1e::1) [AS109] 120.590 ms 120.882 ms 120.842 ms 19 rcdn9-cd2-dmzdcc-gw2-por1.cisco.com (2001:420:1100:1::1) [AS109] 121.705 ms 121.589 ms 121.554 ms 20 rcdn9-14b-dcz05n-gw1-por2.cisco.com (2001:420:1100:10d::1) [AS109] 120.188 ms 120.167 ms 120.289 ms 21 2001:420:1101:1::185 (2001:420:1101:1::185) [AS109] 120.263 ms 120.166 ms 120.133 ms |
That’s it. God bless!
Featured image “Who” by Adrian Scottow is licensed under CC BY-SA 2.0.


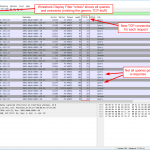
TCP “reassembly on” dissection error (WHOIS)
https://gitlab.com/wireshark/wireshark/-/issues/18037
Fix for missing responses in slide #2.
Wow!!! Thanks for that.