It’s not always this simple DNS thing such as “single query – single answer, both via UDP”. Sometimes you have some more options or bigger messages that look and behave differently on the network. For example: IP fragmentation for larger DNS answers that do not fit into a single UDP datagram (hopefully not after the DNS flag day 2020 anymore), or DNS via TCP, or some newer options within the EDNS space such as “EDNS Client Subnet” (ECS) or DNS cookies.
I won’t explain any details about those options, but I am publishing a pcap with that kind of packets along with some Wireshark screenshots. Feel free to dig into it.
(Please note that I have a couple of downloadable pcaps on my blog, especially this one which looks at DNS and DNSSEC packets. However, with this post here I am looking into other DNS details.)
Download the pcap capture file here. 7zipped, 7 KB:
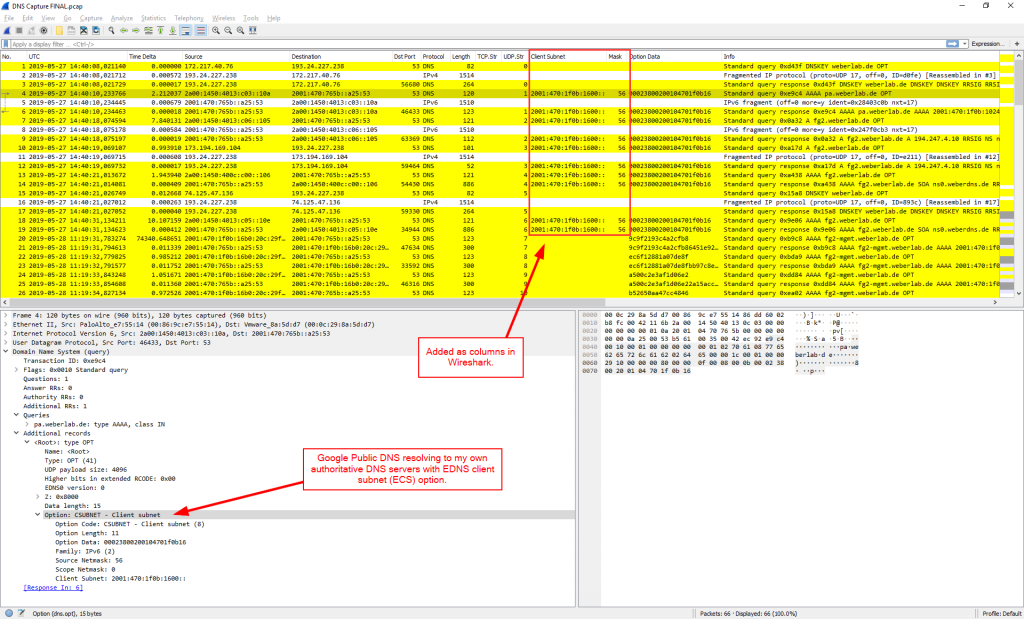
I am using dig version 9.11.3-1ubuntu1.7 (former versions are not using the EDNS cookie) on a Ubuntu 18.04.2 LTS. The Wireshark screenshots are from version 3.0.2. Note my custom Wireshark columns to show some special packet details that are relevant for DNS, likewise the TCP.Stream and UDP.Stream columns.
Common DNS: UDP
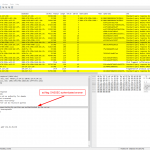
Find some very basic DNS queries/responses in UDP streams 11-14. First one with the “ad” flag (authentic data via DNSSEC), second one with DNSSEC failure aka SERVFAIL. Third and fourth: A and AAAA records:
|
1 2 3 4 |
dig @2606:4700:4700::1111 sigok.verteiltesysteme.net dig @2606:4700:4700::1111 sigfail.verteiltesysteme.net dig @2620:fe::fe formel1.de dig @2620:fe::fe erfpop.de aaaa |
Full listing:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 |
weberjoh@vm22-lx2:~$ dig @2606:4700:4700::1111 sigok.verteiltesysteme.net ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2606:4700:4700::1111 sigok.verteiltesysteme.net ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 37343 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 1452 ;; QUESTION SECTION: ;sigok.verteiltesysteme.net. IN A ;; ANSWER SECTION: sigok.verteiltesysteme.net. 60 IN A 134.91.78.139 ;; Query time: 17 msec ;; SERVER: 2606:4700:4700::1111#53(2606:4700:4700::1111) ;; WHEN: Tue Jun 18 14:58:02 UTC 2019 ;; MSG SIZE rcvd: 71 weberjoh@vm22-lx2:~$ dig @2606:4700:4700::1111 sigfail.verteiltesysteme.net ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2606:4700:4700::1111 sigfail.verteiltesysteme.net ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 64199 ;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0 ;; QUESTION SECTION: ;sigfail.verteiltesysteme.net. IN A ;; Query time: 29 msec ;; SERVER: 2606:4700:4700::1111#53(2606:4700:4700::1111) ;; WHEN: Tue Jun 18 14:58:06 UTC 2019 ;; MSG SIZE rcvd: 46 weberjoh@vm22-lx2:~$ dig @2620:fe::fe formel1.de ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2620:fe::fe formel1.de ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 1764 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;formel1.de. IN A ;; ANSWER SECTION: formel1.de. 3600 IN A 85.25.234.253 ;; Query time: 19 msec ;; SERVER: 2620:fe::fe#53(2620:fe::fe) ;; WHEN: Tue Jun 18 14:58:09 UTC 2019 ;; MSG SIZE rcvd: 55 weberjoh@vm22-lx2:~$ dig @2620:fe::fe erfpop.de aaaa ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2620:fe::fe erfpop.de aaaa ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 36076 ;; flags: qr rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;erfpop.de. IN AAAA ;; ANSWER SECTION: erfpop.de. 300 IN AAAA 2606:4700:30::6818:6291 erfpop.de. 300 IN AAAA 2606:4700:30::6818:6391 ;; Query time: 24 msec ;; SERVER: 2620:fe::fe#53(2620:fe::fe) ;; WHEN: Tue Jun 18 14:58:15 UTC 2019 ;; MSG SIZE rcvd: 94 |
Wireshark screenshots (quite boring at this time ;D):
Bigger Sizes: IP Fragmentation & TCP
Now it’s getting a bit more interesting. Querying for records that are bigger in size requires either IP fragmentation (there is no fragmentation in UDP, hence IP must do it) or the fallback/usage of TCP with its basic three-way handshake. Note that IP fragmentation behaves a bit different for IPv4 and IPv6. At least for IPv6 there is a huge discussion whether this fragmentation header should be dropped at *any* border router/firewall anyway. Keep that in mind when troubleshooting it! Links:
- RFC 7872: Observations on the Dropping of Packets with IPv6 Extension Headers in the Real World
- Enno Rey: Some Notes on the “Drop IPv6 Fragments” vs. “This Will Break DNS[SEC]” Debate
- Geoff Huston: Dealing with IPv6 fragmentation in the DNS, and Part 2
At least TCP is straightforward and without problems. (Note that zone transfers via AXFR and IXFR are handled by TCP by default.) For my test queries I used IPv6 and legacy IP, both via UDP (forcing IP fragmentation) and TCP:
|
1 2 3 4 |
dig -6 @ns1.weberdns.de weberlab.de dnskey +dnssec +notcp dig -4 @ns1.weberdns.de weberlab.de dnskey +dnssec +notcp dig -6 @ns2.weberdns.de weberlab.de dnskey +dnssec +tcp dig -4 @ns2.weberdns.de weberlab.de dnskey +dnssec +tcp |
Full listing (quite long dnskeys, not of interest):
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 |
weberjoh@vm22-lx2:~$ dig -6 @ns1.weberdns.de weberlab.de dnskey +dnssec +notcp ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> -6 @ns1.weberdns.de weberlab.de dnskey +dnssec +notcp ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 49824 ;; flags: qr aa rd; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 1 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags: do; udp: 4096 ; COOKIE: f16ce6e62f7d465c2a33773e5d08fc11654e05c083606c96 (good) ;; QUESTION SECTION: ;weberlab.de. IN DNSKEY ;; ANSWER SECTION: weberlab.de. 60 IN DNSKEY 257 3 10 AwEAAd3v/e0irXYKOwtYEB3VPe7z99qvi5le9/y1XXyplp5y/5xaqrm/ relG8pgx8GsNW2IgviJKAJ6UiU45ERKoH+fz2qf2SUFHFWwkweiWyLZ4 EZHhowviCEx94P4OswNKXmdYHe38rlHPa+3OypW9gYfR9lhCKK3neCPq 8/aFFsTTI7dQ+Q2kERWiCMCybl4WOwsBo/RlnPM4yufMKIlABiM5NWQP NmI6jYzAYpYoyUhd9HnnIIDlNQ89HpXQdFmysMraXYb7qDOoOEiOodtt KH0y/vtJ2SRU05RF4AEumacIUzAi5LL2cMQxC7t7rlDI4X42NRfOLAqG uOeclFjzqz3OdAJWeg/AAnSbb02AGCkQ370TX1hWveAXt6xpPWOLgHXS LIF/lz+wl+Dm8ZNWDnn5zEJuEj3xova1g8zmRXJOmqA6VhGqewxF8c+y KeNEOHz4X4/RLmWHIuEbvboP00Dk5A9bhyZGVsytOJg+NwhFQtvBWLmD 82FFtfSt2vmbFFNwAZOnRZWJOG9L7TFcGIm1OEULmohUyFLsBGMXDFOu 1k0o6pqm495tsBuMyJNpfdQoPwOkUpsKi6jmNq6vRjvvNiJbcFylTQrq HGTGuOopuUsBbUXj/nOr4I6j42k6GDIuTyLDkaVrdrxXmGnfNnStdqWm vHXo/YFwdls9bcT7 weberlab.de. 60 IN DNSKEY 256 3 10 AwEAAdBU3CjxUKw7SeYza7cxyq/Xg3znVQsMzuF/UeLaigOubtJHhxhL +m129IxQkTKo8JRIXcKXD+aViztiml8+8BPCXFNPftFpdFCzBRNGHj/c a1g/Flck6v5avafB/hGqbWKY2LEGKb5ktYWGj8JB0mrKGqDZVPyieC0d YVv02iOaOvUhdl7QtgVybR3V6gHlhoG0BxG+GbjUp+NyPClbuMOIwflb VGB5946PyQGQgnGNX2L1MHumOaYC/D3UnyzQZNMmqj85GwDNPwEeDfLq 6wm1BUfx7MwwcEVuO2B0YmUyiPiSfUoGTwm2P1nGNMhlYij3bY9VvyxC qPQnK0s5Tr0= weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 13179 weberlab.de. w2TKIWrDQs3Wcvql0/ovRLl/4p5WqB3JKD0OqWVDOeRziol1sGwhdm4E dr02rZbX4HUDGLIxy2/cvP/CtesdWyDaO4x4T4YkN5mT54UQ2wvNff5o PwwCZRH6OPzyB66Gjlx5BLMXJQN0n5eV86jGPHSCIwjEiEaIZqc92o3d YPEOZz4b67ok4t625JGhbrwLuiQWs0sb6ZQUxkbC4sA/5Hk9R9HIewVX NaGesZpKsuvLyLA+txY9a9T67e6Zqwh0wrhILDu/A/XQkLlgi5CUMRlF VyY+QiNx7+8RRYKbtlnSuxIhAR+ax6YY2/ISTxXqdXIIM4HUju4K+Dy9 elECeKWhVhKL5UkkijegqldCpc2OVCqaAuGznETIoro5HIC0XCcwzY03 D+fevfXokQWHJ0lDbuzUfwEDrC3tYHBgTGFSNvLlwAYoxSST1GEBRUSi kGGMu1PGroH6HSQpTTPuT4w6ze1VGqMlvwrWxYoC2Wo3v0myxZKHfaE5 LoZ3rS+38hJ5Rn8SphGdtfKj3LCgyUa0cspnPlnWfrT3Gb0F6+gFUu0W UqFE1f/uXVXdpFrrhdsOa7JwCDlN8MCBD4bE8KvZ44W/QafYzjB9xRW6 OLKzb2OKaHDrPS4nNTrPNd27u1ckM9za7/8Xzzj77xv/7n3DxDtdxZwe 3cIP8pk3nrs= weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 36935 weberlab.de. pTxMnEVpxiufOPOuJsnKHMj89lMzzWjszQ3ndtWEaKP73OElE16hQbZl uEkBQwQEC7uB5qnEntTXP5SqGQVKLxC7qNE6cyKHnHOaLFc6M7ZGIdPx 4zNAweqKWt57GZ3P7usfiMKCCkCDZh6dEzOm+Gt/T44RZQ2HCrp01hWU 1aDVh/WjEJGxnpeKral6aV7go6SChtYQKB0QtoychkpQnRa2kBkm4JsA g+9qTdiAdw09HhJvHWUpFM9bpDGMWwcnlf8HqY0xW2ob3vDNo7+6BXAf zVC3YuWmPlZvzvcC0xt3s5BgvCEnt+HEn3E0mfpKVVGnoL7U/ZbK7/tT SaA/6w== ;; Query time: 10 msec ;; SERVER: 2001:470:765b::a25:53#53(2001:470:765b::a25:53) ;; WHEN: Tue Jun 18 14:58:25 UTC 2019 ;; MSG SIZE rcvd: 1730 weberjoh@vm22-lx2:~$ dig -4 @ns1.weberdns.de weberlab.de dnskey +dnssec +notcp ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> -4 @ns1.weberdns.de weberlab.de dnskey +dnssec +notcp ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 35278 ;; flags: qr aa rd; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 1 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags: do; udp: 4096 ; COOKIE: 1dc404dc580e966c943e15565d08fc16a4345a7a72133f61 (good) ;; QUESTION SECTION: ;weberlab.de. IN DNSKEY ;; ANSWER SECTION: weberlab.de. 60 IN DNSKEY 256 3 10 AwEAAdBU3CjxUKw7SeYza7cxyq/Xg3znVQsMzuF/UeLaigOubtJHhxhL +m129IxQkTKo8JRIXcKXD+aViztiml8+8BPCXFNPftFpdFCzBRNGHj/c a1g/Flck6v5avafB/hGqbWKY2LEGKb5ktYWGj8JB0mrKGqDZVPyieC0d YVv02iOaOvUhdl7QtgVybR3V6gHlhoG0BxG+GbjUp+NyPClbuMOIwflb VGB5946PyQGQgnGNX2L1MHumOaYC/D3UnyzQZNMmqj85GwDNPwEeDfLq 6wm1BUfx7MwwcEVuO2B0YmUyiPiSfUoGTwm2P1nGNMhlYij3bY9VvyxC qPQnK0s5Tr0= weberlab.de. 60 IN DNSKEY 257 3 10 AwEAAd3v/e0irXYKOwtYEB3VPe7z99qvi5le9/y1XXyplp5y/5xaqrm/ relG8pgx8GsNW2IgviJKAJ6UiU45ERKoH+fz2qf2SUFHFWwkweiWyLZ4 EZHhowviCEx94P4OswNKXmdYHe38rlHPa+3OypW9gYfR9lhCKK3neCPq 8/aFFsTTI7dQ+Q2kERWiCMCybl4WOwsBo/RlnPM4yufMKIlABiM5NWQP NmI6jYzAYpYoyUhd9HnnIIDlNQ89HpXQdFmysMraXYb7qDOoOEiOodtt KH0y/vtJ2SRU05RF4AEumacIUzAi5LL2cMQxC7t7rlDI4X42NRfOLAqG uOeclFjzqz3OdAJWeg/AAnSbb02AGCkQ370TX1hWveAXt6xpPWOLgHXS LIF/lz+wl+Dm8ZNWDnn5zEJuEj3xova1g8zmRXJOmqA6VhGqewxF8c+y KeNEOHz4X4/RLmWHIuEbvboP00Dk5A9bhyZGVsytOJg+NwhFQtvBWLmD 82FFtfSt2vmbFFNwAZOnRZWJOG9L7TFcGIm1OEULmohUyFLsBGMXDFOu 1k0o6pqm495tsBuMyJNpfdQoPwOkUpsKi6jmNq6vRjvvNiJbcFylTQrq HGTGuOopuUsBbUXj/nOr4I6j42k6GDIuTyLDkaVrdrxXmGnfNnStdqWm vHXo/YFwdls9bcT7 weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 13179 weberlab.de. w2TKIWrDQs3Wcvql0/ovRLl/4p5WqB3JKD0OqWVDOeRziol1sGwhdm4E dr02rZbX4HUDGLIxy2/cvP/CtesdWyDaO4x4T4YkN5mT54UQ2wvNff5o PwwCZRH6OPzyB66Gjlx5BLMXJQN0n5eV86jGPHSCIwjEiEaIZqc92o3d YPEOZz4b67ok4t625JGhbrwLuiQWs0sb6ZQUxkbC4sA/5Hk9R9HIewVX NaGesZpKsuvLyLA+txY9a9T67e6Zqwh0wrhILDu/A/XQkLlgi5CUMRlF VyY+QiNx7+8RRYKbtlnSuxIhAR+ax6YY2/ISTxXqdXIIM4HUju4K+Dy9 elECeKWhVhKL5UkkijegqldCpc2OVCqaAuGznETIoro5HIC0XCcwzY03 D+fevfXokQWHJ0lDbuzUfwEDrC3tYHBgTGFSNvLlwAYoxSST1GEBRUSi kGGMu1PGroH6HSQpTTPuT4w6ze1VGqMlvwrWxYoC2Wo3v0myxZKHfaE5 LoZ3rS+38hJ5Rn8SphGdtfKj3LCgyUa0cspnPlnWfrT3Gb0F6+gFUu0W UqFE1f/uXVXdpFrrhdsOa7JwCDlN8MCBD4bE8KvZ44W/QafYzjB9xRW6 OLKzb2OKaHDrPS4nNTrPNd27u1ckM9za7/8Xzzj77xv/7n3DxDtdxZwe 3cIP8pk3nrs= weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 36935 weberlab.de. pTxMnEVpxiufOPOuJsnKHMj89lMzzWjszQ3ndtWEaKP73OElE16hQbZl uEkBQwQEC7uB5qnEntTXP5SqGQVKLxC7qNE6cyKHnHOaLFc6M7ZGIdPx 4zNAweqKWt57GZ3P7usfiMKCCkCDZh6dEzOm+Gt/T44RZQ2HCrp01hWU 1aDVh/WjEJGxnpeKral6aV7go6SChtYQKB0QtoychkpQnRa2kBkm4JsA g+9qTdiAdw09HhJvHWUpFM9bpDGMWwcnlf8HqY0xW2ob3vDNo7+6BXAf zVC3YuWmPlZvzvcC0xt3s5BgvCEnt+HEn3E0mfpKVVGnoL7U/ZbK7/tT SaA/6w== ;; Query time: 13 msec ;; SERVER: 193.24.227.238#53(193.24.227.238) ;; WHEN: Tue Jun 18 14:58:30 UTC 2019 ;; MSG SIZE rcvd: 1730 weberjoh@vm22-lx2:~$ dig -6 @ns2.weberdns.de weberlab.de dnskey +dnssec +tcp ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> -6 @ns2.weberdns.de weberlab.de dnskey +dnssec +tcp ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 32996 ;; flags: qr aa rd; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 1 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags: do; udp: 4096 ; COOKIE: 1b9af622ab2c9740e40584c05d08fc19f07835a115ea8294 (good) ;; QUESTION SECTION: ;weberlab.de. IN DNSKEY ;; ANSWER SECTION: weberlab.de. 60 IN DNSKEY 256 3 10 AwEAAdBU3CjxUKw7SeYza7cxyq/Xg3znVQsMzuF/UeLaigOubtJHhxhL +m129IxQkTKo8JRIXcKXD+aViztiml8+8BPCXFNPftFpdFCzBRNGHj/c a1g/Flck6v5avafB/hGqbWKY2LEGKb5ktYWGj8JB0mrKGqDZVPyieC0d YVv02iOaOvUhdl7QtgVybR3V6gHlhoG0BxG+GbjUp+NyPClbuMOIwflb VGB5946PyQGQgnGNX2L1MHumOaYC/D3UnyzQZNMmqj85GwDNPwEeDfLq 6wm1BUfx7MwwcEVuO2B0YmUyiPiSfUoGTwm2P1nGNMhlYij3bY9VvyxC qPQnK0s5Tr0= weberlab.de. 60 IN DNSKEY 257 3 10 AwEAAd3v/e0irXYKOwtYEB3VPe7z99qvi5le9/y1XXyplp5y/5xaqrm/ relG8pgx8GsNW2IgviJKAJ6UiU45ERKoH+fz2qf2SUFHFWwkweiWyLZ4 EZHhowviCEx94P4OswNKXmdYHe38rlHPa+3OypW9gYfR9lhCKK3neCPq 8/aFFsTTI7dQ+Q2kERWiCMCybl4WOwsBo/RlnPM4yufMKIlABiM5NWQP NmI6jYzAYpYoyUhd9HnnIIDlNQ89HpXQdFmysMraXYb7qDOoOEiOodtt KH0y/vtJ2SRU05RF4AEumacIUzAi5LL2cMQxC7t7rlDI4X42NRfOLAqG uOeclFjzqz3OdAJWeg/AAnSbb02AGCkQ370TX1hWveAXt6xpPWOLgHXS LIF/lz+wl+Dm8ZNWDnn5zEJuEj3xova1g8zmRXJOmqA6VhGqewxF8c+y KeNEOHz4X4/RLmWHIuEbvboP00Dk5A9bhyZGVsytOJg+NwhFQtvBWLmD 82FFtfSt2vmbFFNwAZOnRZWJOG9L7TFcGIm1OEULmohUyFLsBGMXDFOu 1k0o6pqm495tsBuMyJNpfdQoPwOkUpsKi6jmNq6vRjvvNiJbcFylTQrq HGTGuOopuUsBbUXj/nOr4I6j42k6GDIuTyLDkaVrdrxXmGnfNnStdqWm vHXo/YFwdls9bcT7 weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 13179 weberlab.de. w2TKIWrDQs3Wcvql0/ovRLl/4p5WqB3JKD0OqWVDOeRziol1sGwhdm4E dr02rZbX4HUDGLIxy2/cvP/CtesdWyDaO4x4T4YkN5mT54UQ2wvNff5o PwwCZRH6OPzyB66Gjlx5BLMXJQN0n5eV86jGPHSCIwjEiEaIZqc92o3d YPEOZz4b67ok4t625JGhbrwLuiQWs0sb6ZQUxkbC4sA/5Hk9R9HIewVX NaGesZpKsuvLyLA+txY9a9T67e6Zqwh0wrhILDu/A/XQkLlgi5CUMRlF VyY+QiNx7+8RRYKbtlnSuxIhAR+ax6YY2/ISTxXqdXIIM4HUju4K+Dy9 elECeKWhVhKL5UkkijegqldCpc2OVCqaAuGznETIoro5HIC0XCcwzY03 D+fevfXokQWHJ0lDbuzUfwEDrC3tYHBgTGFSNvLlwAYoxSST1GEBRUSi kGGMu1PGroH6HSQpTTPuT4w6ze1VGqMlvwrWxYoC2Wo3v0myxZKHfaE5 LoZ3rS+38hJ5Rn8SphGdtfKj3LCgyUa0cspnPlnWfrT3Gb0F6+gFUu0W UqFE1f/uXVXdpFrrhdsOa7JwCDlN8MCBD4bE8KvZ44W/QafYzjB9xRW6 OLKzb2OKaHDrPS4nNTrPNd27u1ckM9za7/8Xzzj77xv/7n3DxDtdxZwe 3cIP8pk3nrs= weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 36935 weberlab.de. pTxMnEVpxiufOPOuJsnKHMj89lMzzWjszQ3ndtWEaKP73OElE16hQbZl uEkBQwQEC7uB5qnEntTXP5SqGQVKLxC7qNE6cyKHnHOaLFc6M7ZGIdPx 4zNAweqKWt57GZ3P7usfiMKCCkCDZh6dEzOm+Gt/T44RZQ2HCrp01hWU 1aDVh/WjEJGxnpeKral6aV7go6SChtYQKB0QtoychkpQnRa2kBkm4JsA g+9qTdiAdw09HhJvHWUpFM9bpDGMWwcnlf8HqY0xW2ob3vDNo7+6BXAf zVC3YuWmPlZvzvcC0xt3s5BgvCEnt+HEn3E0mfpKVVGnoL7U/ZbK7/tT SaA/6w== ;; Query time: 0 msec ;; SERVER: 2001:470:1f0b:16b0::a26:53#53(2001:470:1f0b:16b0::a26:53) ;; WHEN: Tue Jun 18 14:58:33 UTC 2019 ;; MSG SIZE rcvd: 1730 weberjoh@vm22-lx2:~$ dig -4 @ns2.weberdns.de weberlab.de dnskey +dnssec +tcp ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> -4 @ns2.weberdns.de weberlab.de dnskey +dnssec +tcp ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 1754 ;; flags: qr aa rd; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 1 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags: do; udp: 4096 ; COOKIE: c6ab1a7fa365f223dd0e36455d08fc1c37dacb4464d60422 (good) ;; QUESTION SECTION: ;weberlab.de. IN DNSKEY ;; ANSWER SECTION: weberlab.de. 60 IN DNSKEY 257 3 10 AwEAAd3v/e0irXYKOwtYEB3VPe7z99qvi5le9/y1XXyplp5y/5xaqrm/ relG8pgx8GsNW2IgviJKAJ6UiU45ERKoH+fz2qf2SUFHFWwkweiWyLZ4 EZHhowviCEx94P4OswNKXmdYHe38rlHPa+3OypW9gYfR9lhCKK3neCPq 8/aFFsTTI7dQ+Q2kERWiCMCybl4WOwsBo/RlnPM4yufMKIlABiM5NWQP NmI6jYzAYpYoyUhd9HnnIIDlNQ89HpXQdFmysMraXYb7qDOoOEiOodtt KH0y/vtJ2SRU05RF4AEumacIUzAi5LL2cMQxC7t7rlDI4X42NRfOLAqG uOeclFjzqz3OdAJWeg/AAnSbb02AGCkQ370TX1hWveAXt6xpPWOLgHXS LIF/lz+wl+Dm8ZNWDnn5zEJuEj3xova1g8zmRXJOmqA6VhGqewxF8c+y KeNEOHz4X4/RLmWHIuEbvboP00Dk5A9bhyZGVsytOJg+NwhFQtvBWLmD 82FFtfSt2vmbFFNwAZOnRZWJOG9L7TFcGIm1OEULmohUyFLsBGMXDFOu 1k0o6pqm495tsBuMyJNpfdQoPwOkUpsKi6jmNq6vRjvvNiJbcFylTQrq HGTGuOopuUsBbUXj/nOr4I6j42k6GDIuTyLDkaVrdrxXmGnfNnStdqWm vHXo/YFwdls9bcT7 weberlab.de. 60 IN DNSKEY 256 3 10 AwEAAdBU3CjxUKw7SeYza7cxyq/Xg3znVQsMzuF/UeLaigOubtJHhxhL +m129IxQkTKo8JRIXcKXD+aViztiml8+8BPCXFNPftFpdFCzBRNGHj/c a1g/Flck6v5avafB/hGqbWKY2LEGKb5ktYWGj8JB0mrKGqDZVPyieC0d YVv02iOaOvUhdl7QtgVybR3V6gHlhoG0BxG+GbjUp+NyPClbuMOIwflb VGB5946PyQGQgnGNX2L1MHumOaYC/D3UnyzQZNMmqj85GwDNPwEeDfLq 6wm1BUfx7MwwcEVuO2B0YmUyiPiSfUoGTwm2P1nGNMhlYij3bY9VvyxC qPQnK0s5Tr0= weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 13179 weberlab.de. w2TKIWrDQs3Wcvql0/ovRLl/4p5WqB3JKD0OqWVDOeRziol1sGwhdm4E dr02rZbX4HUDGLIxy2/cvP/CtesdWyDaO4x4T4YkN5mT54UQ2wvNff5o PwwCZRH6OPzyB66Gjlx5BLMXJQN0n5eV86jGPHSCIwjEiEaIZqc92o3d YPEOZz4b67ok4t625JGhbrwLuiQWs0sb6ZQUxkbC4sA/5Hk9R9HIewVX NaGesZpKsuvLyLA+txY9a9T67e6Zqwh0wrhILDu/A/XQkLlgi5CUMRlF VyY+QiNx7+8RRYKbtlnSuxIhAR+ax6YY2/ISTxXqdXIIM4HUju4K+Dy9 elECeKWhVhKL5UkkijegqldCpc2OVCqaAuGznETIoro5HIC0XCcwzY03 D+fevfXokQWHJ0lDbuzUfwEDrC3tYHBgTGFSNvLlwAYoxSST1GEBRUSi kGGMu1PGroH6HSQpTTPuT4w6ze1VGqMlvwrWxYoC2Wo3v0myxZKHfaE5 LoZ3rS+38hJ5Rn8SphGdtfKj3LCgyUa0cspnPlnWfrT3Gb0F6+gFUu0W UqFE1f/uXVXdpFrrhdsOa7JwCDlN8MCBD4bE8KvZ44W/QafYzjB9xRW6 OLKzb2OKaHDrPS4nNTrPNd27u1ckM9za7/8Xzzj77xv/7n3DxDtdxZwe 3cIP8pk3nrs= weberlab.de. 60 IN RRSIG DNSKEY 10 2 60 20190711220120 20190611215721 36935 weberlab.de. pTxMnEVpxiufOPOuJsnKHMj89lMzzWjszQ3ndtWEaKP73OElE16hQbZl uEkBQwQEC7uB5qnEntTXP5SqGQVKLxC7qNE6cyKHnHOaLFc6M7ZGIdPx 4zNAweqKWt57GZ3P7usfiMKCCkCDZh6dEzOm+Gt/T44RZQ2HCrp01hWU 1aDVh/WjEJGxnpeKral6aV7go6SChtYQKB0QtoychkpQnRa2kBkm4JsA g+9qTdiAdw09HhJvHWUpFM9bpDGMWwcnlf8HqY0xW2ob3vDNo7+6BXAf zVC3YuWmPlZvzvcC0xt3s5BgvCEnt+HEn3E0mfpKVVGnoL7U/ZbK7/tT SaA/6w== ;; Query time: 0 msec ;; SERVER: 194.247.5.14#53(194.247.5.14) ;; WHEN: Tue Jun 18 14:58:36 UTC 2019 ;; MSG SIZE rcvd: 1730 weberjoh@vm22-lx2:~$ |
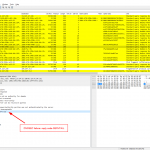
Find those two UDP with IP fragmentation sessions at UDP streams 15 & 16 (while those IP fragments are NOT part of the stream directly. Again, be careful!) and TCP streams 0 and 1:
Fun fact out of my daily business while dealing with shitty fragments:
Grr. Just failed in capturing DNS traffic with "port 53" tcpdump filter. Why? Because #IPv6 fragment is not "port 53". Took me 1 hour!!! pic.twitter.com/xepm0G9OTF
— Johannes Weber 🎸 (@webernetz) October 10, 2017
EDNS Extensions
The extension mechanisms for DNS (EDNS), RFC 6891, offer a flexible way to increase the DNS features. I am showing two scenarios here: RFC 7871 “Client Subnet in DNS Queries” and RFC 7873 “Domain Name System (DNS) Cookies”.
EDNS(0) Client Subnet
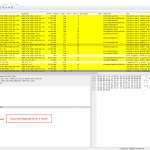
For the EDNS client subnet (ECS) packets I queried the Google Public DNS Resolver from one of my Linux machines, but I captured the packets on my authoritative DNS server! That is: The packets in the trace file show the resolving process from Google Public DNS to my DNS server ns1.weberdns.de. Google adds the client subnet, which in this case is a /56 IPv6 prefix on which my Linux machine resides.
|
1 2 3 4 |
dig @2001:4860:4860::8888 pa.weberlab.de dig @2001:4860:4860::8888 pa.weberlab.de aaaa dig @2001:4860:4860::8888 fg2.weberlab.de dig @2001:4860:4860::8888 fg2.weberlab.de aaaa |
Full listing (nothing to see here, skip it):
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 |
weberjoh@vm22-lx2:~$ dig @2001:4860:4860::8888 pa.weberlab.de ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2001:4860:4860::8888 pa.weberlab.de ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 43536 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;pa.weberlab.de. IN A ;; ANSWER SECTION: pa.weberlab.de. 59 IN A 193.24.227.9 ;; Query time: 1068 msec ;; SERVER: 2001:4860:4860::8888#53(2001:4860:4860::8888) ;; WHEN: Mon May 27 14:40:08 UTC 2019 ;; MSG SIZE rcvd: 59 weberjoh@vm22-lx2:~$ dig @2001:4860:4860::8888 pa.weberlab.de aaaa ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2001:4860:4860::8888 pa.weberlab.de aaaa ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 16871 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;pa.weberlab.de. IN AAAA ;; ANSWER SECTION: pa.weberlab.de. 59 IN AAAA 2001:470:1f0b:1024::2 ;; Query time: 1036 msec ;; SERVER: 2001:4860:4860::8888#53(2001:4860:4860::8888) ;; WHEN: Mon May 27 14:40:11 UTC 2019 ;; MSG SIZE rcvd: 71 weberjoh@vm22-lx2:~$ dig @2001:4860:4860::8888 fg2.weberlab.de ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2001:4860:4860::8888 fg2.weberlab.de ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 63678 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;fg2.weberlab.de. IN A ;; ANSWER SECTION: fg2.weberlab.de. 59 IN A 194.247.4.10 ;; Query time: 2080 msec ;; SERVER: 2001:4860:4860::8888#53(2001:4860:4860::8888) ;; WHEN: Mon May 27 14:40:19 UTC 2019 ;; MSG SIZE rcvd: 60 weberjoh@vm22-lx2:~$ dig @2001:4860:4860::8888 fg2.weberlab.de aaaa ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @2001:4860:4860::8888 fg2.weberlab.de aaaa ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 14923 ;; flags: qr rd ra ad; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;fg2.weberlab.de. IN AAAA ;; AUTHORITY SECTION: weberlab.de. 59 IN SOA ns0.weberdns.de. webmaster.webernetz.net. 2019051753 3600 900 2419200 60 ;; Query time: 79 msec ;; SERVER: 2001:4860:4860::8888#53(2001:4860:4860::8888) ;; WHEN: Mon May 27 14:40:21 UTC 2019 ;; MSG SIZE rcvd: 116 |
Not all resolving queries from Google Public DNS are shown here because I only captured on one out of two authoritative DNS servers. However, some queries came in twice, some over IPv6 – some over legacy IP. For whatever reason:
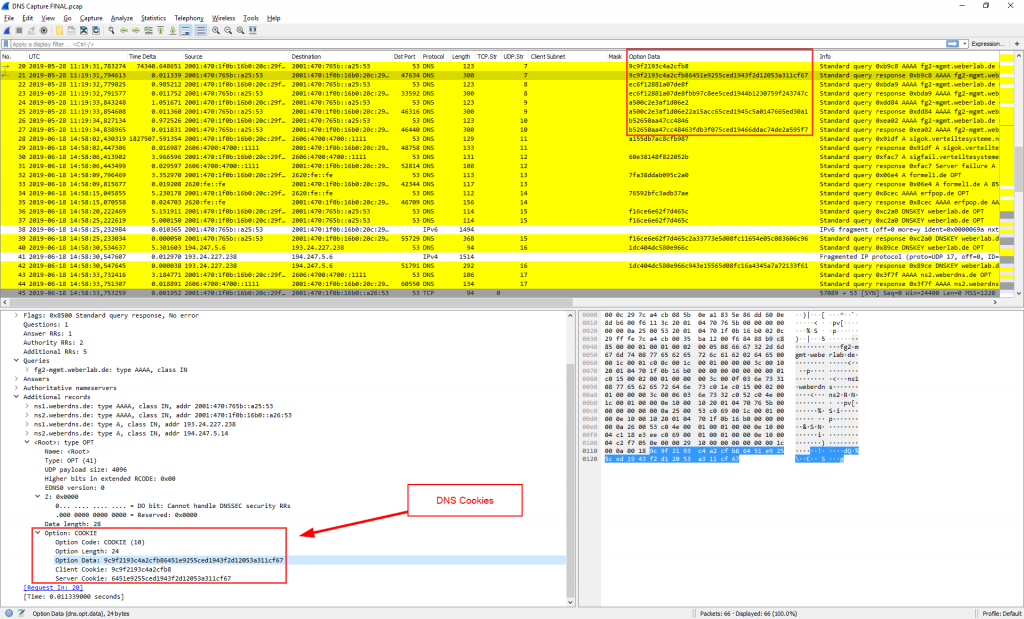
Domain Name System (DNS) Cookies
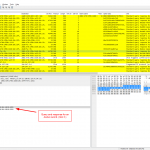
Finally, DNS cookies: “DNS Cookies are a lightweight DNS transaction security mechanism that provides limited protection to DNS servers and clients against a variety of increasingly common denial-of-service and amplification/ forgery or cache poisoning attacks by off-path attackers”, RFC 7873. I simply queried my authoritative DNS server (hence the “aa”, authoritative answer, flag is set) four times for the same FQDN. For every transaction, a new client and server cookie was generated by both sides. UDP streams 7-10.
|
1 2 3 4 |
dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional |
Full listing which also shows the cookies in the dig output:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 |
weberjoh@vm22-lx2:~$ dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; (2 servers found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 47560 ;; flags: qr aa rd; QUERY: 1, ANSWER: 1, AUTHORITY: 2, ADDITIONAL: 5 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ; COOKIE: 9c9f2193c4a2cfb86451e9255ced1943f2d12053a311cf67 (good) ;; QUESTION SECTION: ;fg2-mgmt.weberlab.de. IN AAAA ;; ANSWER SECTION: fg2-mgmt.weberlab.de. 60 IN AAAA 2001:470:1f0b:16b0::1 ;; Query time: 11 msec ;; SERVER: 2001:470:765b::a25:53#53(2001:470:765b::a25:53) ;; WHEN: Tue May 28 11:19:31 UTC 2019 ;; MSG SIZE rcvd: 238 weberjoh@vm22-lx2:~$ dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; (2 servers found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 48553 ;; flags: qr aa rd; QUERY: 1, ANSWER: 1, AUTHORITY: 2, ADDITIONAL: 5 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ; COOKIE: ec6f12881a07de8fbb97c8ee5ced1944b1230759f243747c (good) ;; QUESTION SECTION: ;fg2-mgmt.weberlab.de. IN AAAA ;; ANSWER SECTION: fg2-mgmt.weberlab.de. 60 IN AAAA 2001:470:1f0b:16b0::1 ;; Query time: 11 msec ;; SERVER: 2001:470:765b::a25:53#53(2001:470:765b::a25:53) ;; WHEN: Tue May 28 11:19:32 UTC 2019 ;; MSG SIZE rcvd: 238 weberjoh@vm22-lx2:~$ dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; (2 servers found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 56708 ;; flags: qr aa rd; QUERY: 1, ANSWER: 1, AUTHORITY: 2, ADDITIONAL: 5 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ; COOKIE: a500c2e3af1d06e22a15acc65ced1945c5a0147665ed30a1 (good) ;; QUESTION SECTION: ;fg2-mgmt.weberlab.de. IN AAAA ;; ANSWER SECTION: fg2-mgmt.weberlab.de. 60 IN AAAA 2001:470:1f0b:16b0::1 ;; Query time: 11 msec ;; SERVER: 2001:470:765b::a25:53#53(2001:470:765b::a25:53) ;; WHEN: Tue May 28 11:19:33 UTC 2019 ;; MSG SIZE rcvd: 238 weberjoh@vm22-lx2:~$ dig @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> @ns1.weberdns.de fg2-mgmt.weberlab.de aaaa +noauthority +noadditional ; (2 servers found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 59906 ;; flags: qr aa rd; QUERY: 1, ANSWER: 1, AUTHORITY: 2, ADDITIONAL: 5 ;; WARNING: recursion requested but not available ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ; COOKIE: b52650aa47cc48463fdb3f075ced19466ddac74de2a595f7 (good) ;; QUESTION SECTION: ;fg2-mgmt.weberlab.de. IN AAAA ;; ANSWER SECTION: fg2-mgmt.weberlab.de. 60 IN AAAA 2001:470:1f0b:16b0::1 ;; Query time: 11 msec ;; SERVER: 2001:470:765b::a25:53#53(2001:470:765b::a25:53) ;; WHEN: Tue May 28 11:19:34 UTC 2019 ;; MSG SIZE rcvd: 238 |
Wireshark screenshot, again with a custom column:
That’s it. Happy wiresharking!
Further Links
- CDNPlanet – Which CDNs support edns-client-subnet?
- Google Public DNS – EDNS Client Subnet (ECS) Guidelines
Featured image “Shirley Lo” by Thomas Hawk is licensed under CC BY-NC 2.0.