Since a couple of months, I am carrying a ProfiShark 1G always with me. It’s a small network aggregation TAP that fits into my bag (unlike almost any other TAPs or switches with SPAN functionalities). It runs solely via USB 3.0, hence no additional power supply nor network port on my laptop is required to get it running.
In this post, I’ll give some hints on how to use the ProfiShark 1G with Windows (read: some initial problems I had and how to solve them) as well as some use cases out of my daily work with it.
Some other guys already published a couple of technical blogposts concerning the ProfiShark such as A look at a portable USB3 network TAP and A look at the Profishark 1G+. They all go into detail about the general features of the ProfiShark, so I won’t repeat them here.
Hardware
Not much to say about the hardware: A tiny box with two network ports (A and B) for using it inline or for capturing dual SPAN, as well as a USB 3.0 port to plug it into your computer. Some LEDs and no DIP switches that could confuse you. However, I am not using the delivered USB and network cables but shorter ones to even save more space within my bag. That is: a 1 meter flat USB 3.0 cable as well as a 1 meter flat (but Cat 6A) network cable. Both fit into the ProfiShark pocket which gives you a single package to carry. Nice.
Driver and Ethernet Adapters
Two small problems I faced during my first weeks with the ProfiShark 1G:
First: For every USB port to which the ProfiShark is connected, a new network card is installed by Windows. Hence I was a bit confused as I plugged it into another USB port and got another “Ethernet 9” or whatever number. The irritating point was that I needed to restart the WinPCAP driver (or reboot the machine) each time a new Ethernet adapter was installed in order to use it in Wireshark. One day I was like “why can’t I see my ProfiShark as I used it just yesterday”, until I saw that I used another USB port. In the following two screenshots you can see that the same ProfiShark is displayed as Ethernet 7 respectively Ethernet 6, dependent on the USB port:
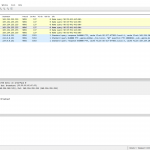
Second: During the initial driver installation from Profitap all protocol checkmarks within the Ethernet adapter are disabled. This is a MUST because otherwise, you get some strange packets in Wireshark since Windows uses the ProfiShark as a “normal” Ethernet adapter. But: As I am using the ProfiShark on different USB ports (which installs more than one adapter, see first point), those checkmarks are NOT disabled by default. You must disable them manually to get rid of some Windows generated packets within the trace files. In other words: I really expected that no single packet is displayed in Wireshark when I am using this TAP. But this was not true until I disabled all checkmarks from the ProfiShark Ethernet adapters. In the following Wireshark screenshot, you can see which packets are “captured” if not all protocols are disabled within the Ethernet section. The other screenshot shows the correctly disabled settings:
Two more hints: I lost some of my ongoing traces as I tried to analyze them in Wireshark while capturing. For some reason, Wireshark crashed and my (unsaved) capture files were lost. Shit. That is: Either don’t touch Wireshark during a packet capture or use the “direct capture” feature within the ProfiShark Manager software. If you’re using the ProfiShark Manager software, keep in mind that all checkboxes react immediately without any further confirmation. Take care especially on the options at Network Ports -> Ports control! If you disable/enable anyone of them while capturing, your ports will probably go down and up again. The “Save” button is just for saving the settings persistently to the flash.
Use Cases
Here are some use cases out of my daily business. All are more or less layer 7 and protocol related. That is, I am not using the additional timestamp dissector from the ProfiShark which gives you an even better time accuracy. I simply don’t need it. And I am not interested in any CRC32 errors as well. I am not troubleshooting layer 1/2/3 issues (as others do) with the TAP but upper-layer problems in one of those generic scenarios:
- When I need to troubleshoot something on a device that has no built-in capturing feature such as printers, VoIP phones, network cameras or any other closed systems.
- When I need to capture packets on a device on which I have no access nor admin privileges at all, that is: customer laptops.
- When I want to capture packets on more than one position at the network simultaneously while using my single notebook. That is: Using the ProfiShark with USB 3.0 on the one side and a common SPAN port via an Ethernet cable on the other side.
- When I want to capture packets on a (network) device without touching it at all.
Here are some concrete examples/problems that I solved using the ProfiShark:
- A customer upgraded its VoIP phones to encrypted RTP streams. We wanted to verify that the voice calls are really encrypted and not transferred via unencrypted RTP (which you can easily replay with Wireshark at Telephony -> VoIP Calls -> Play Streams). We could prove that the encrypted RTP streams are working as expected. Since the ProfiShark supports PoE we could easily inject it before a VoIP phone (scenario 1).
- I was interested in how Apples AirPlay works between my Yamaha network receiver and an iPhone. Obviously, the amp has no built-in capturing feature ;) and the iPhone is wireless. The ProfiShark caught it (scenario 1 again, blogpost here).
- A customer updated its proxy PAC file but a few websites did not display it correctly. We wanted to investigate whether the correct proxy was addressed or not. Since we were not able to install Wireshark on the laptops themselves, we used ProfiShark (scenario 2).
- Using TLS inspection (= MITM) on the Internet-facing firewalls a customer got errors with a 3rd party Java application that uses certificate pinning. We wanted to investigate at which point the TLS connection was blocked by whom. Again, we had no chance to use Wireshark locally on the notebook, hence we used the ProfiShark (scenario 2 again).
- We were facing some unknown latency issues behind a firewall at the customer’s site. Therefore we wanted to capture some connections before AND behind the firewall simultaneously. We used a normal SPAN port on the ISP uplink as well as the ProfiShark behind the firewall. That is: We ran two Wireshark capturing processes at once on the same PC (scenario 3).
- I was interested in what a basic Nmap scan looks like on the wire. Though I could use tcpdump on the laptop that runs Nmap itself, I did not want to touch the process at all. Hence I used the ProfiShark (scenario 4, blogpost here).
- How many port scans from the Internet does my home router thwart per day? I was interested in how many incoming connections terminate at my AVM Fritzbox (a well-known German home router). Though I could use the built-in capturing feature “Paketmitschnitt” I did not want to plug in any end-user device during my packet capture. I captured all connections with the ProfiShark at the ISP-facing interface (scenario 4 again, blogpost here).
If you’re interested in some more posts in which I used the ProfiShark, follow the ProfiShark tag on my blog.
Conclusion
I am really happy with the ProfiShark 1G. It perfectly fits into my bag so I am carrying it with me all the time. It’s always a little surprise for my customers/colleagues when they see it for the first time. You simply don’t expect a complete network TAP inside such a small pocket. And it’s absolutely easy to use of course (despite the very first confusion that I explained above).
Featured image “Great White Shark” by Elias Levy is licensed under CC BY 2.0.








Good post! Regarding Wireshark crashing: Wireshark always writes captured frames to disk; there are almost no frames in memory that are lost when it crashes. You can usually salvage the recent capture files from your temp folder, as described here: https://blog.packet-foo.com/2014/07/wireshark-file-storage/
This does the same trick for a far cheaper price and without USB hassle:
https://greatscottgadgets.com/throwingstar/
;)
The USB feature is absolutely great! You must not sacrifice your Ethernet port. I really like it.
And those cheap “devices” as the throwingstar only work for 100 MBit, but not for 1 GBit. Hence not that usefull anymore nowadays.
Also, the Throwingstar has the additional hassle of requiring TWO LAN ports to capture traffic. That’s more hassle than using a USB device IMHO :-)